- Veille Cyber N593 – 27 avril 2026par veillecybertb le 30 avril 2026 à 13h03
Veille hebdomadaire du 26 avril 2026 CyberStratégie /CyberDéfense / CyberSécurité – Protection des données / RGPD – Intelligence artificielle … Lettre Cyber 593 L’actualité cyber du 20 au 26 avril 2026 …… faits, chroniques et opinions, référentiels, séquences audio, séquences vidéo … selon vos centres d’intérêt, personnels ou professionnels, je vous laisse découvrir l’actualité de la semaine, dans ces domaines essentiels que sont … la CyberStratégie, la CyberSécurité, la protection des données personnelles et l’intelligence artificielle … sans prétention à l’exhaustivité et avec beaucoup de subjectivité, inévitable, bien évidemment. Une bonne semaine à vous. Sans oublier que je reste à l’écoute de vos commentaires et de vos observations guillet.lionel@gmail.com Ce qui a retenu mon attention dans l’actualité de cette semaine 21 avril 2026. Toutes les vidéos des auditions de la Commission d’enquête de l’Assemblée nationale sur les dépendances numériques sont en ligne – L’Agence Nationale des Titres Sécurisés … pas tant que cela, nouvelle fuite massive de données à caractère personnel gérées par un service public, l’ANTS touchée par une cyberattaque – Fuite de données chez Vercel, une plateforme de développement cloud. A l’origine, une application d’IA tierce … A(ré)écouter – A (re)voir Cyberattaques : les collectivités territoriales, particulièrement ciblées, doivent apprendre à résister dans la chronique « Nouveau monde » de Nicolas ARPAGIAN sur FranceInfo (voir aussi la lettre de veille du 19 avril) Toutes les vidéos des auditions de la Commission d’enquête de l’Assemblée nationale sur les dépendances structurelles et les vulnérabilités dans le secteur numérique et les risques pour l’indépendance de la France sont ici … Des ministères cherchent des alternatives aux éditeurs logiciels US Le rapport M-Trends 2026 de Mandiant analysé au micro de l’équipe NoLimitSecu cette semaine avec David GROUT Histoire de la Cyber Française – FSSI, Matignon & Santé avec Philippe Loudenot, une vidéo de son interview Informations Négationnisme, deepfakes, usurpation d’identité… On vous résume les accusations qui visent le réseau X et pour lesquelles Elon Musk est convoqué devant la justice française Affaire X : le bras de fer entre Elon Musk et la justice français entre dans sa phase critique La Commission européenne met 180 millions sur le cloud souverain, voici qui sont les gagnants Loi SREN : le décret attendu qui redéfinit les règles du cloud pour les administrations Management de la sécurité de l’Information Cybersécurité : quand la menace oblige à repenser le périmètre de la sécurité Identités sous pression : quand l’IA et la cryptographie redessinent la surface d’attaque Les réseaux sociaux professionnels, terrain de chasse de nombreux services de renseignement, un livret de sensibilisation de la DGSI, la Direction Générale de la Sécurité Intérieure Sécurité économique : Pourquoi la DGSI recommande aux entreprises de bannir certaines solutions SaaS étrangères (voir aussi la lettre de veille du 19 avril sur le flas ingérence de la DGSI) L’ensemble des interviews du Global Security Mag dans le contexte du Forum InCyber qui a eu lieu du 31 mars au 2 avril ici … Cyberassurance : les conflits de 2026 durcissent les clauses de guerre SOC : comment améliorer l’expérience des analystes et pourquoi c’est important Fuite de données ou violation de données ? Votre stockage en cloud est-il compatible avec l’IA ? Cybersécurité OT et IA, 5 stratégies contre les cybermenaces L’identité est le nouveau périmètre : surmonter les points faibles d’Active Directory Comment la réduction des activités de gestion des CVE par le NIST affecte les équipes de cybersécurité (en) (voir aussi la lettre de veille du 19 avril) La fonction Recall dans Windows reste toujours vulnérable Et puis, dans la vie personnelle comme dans la vie professionnelle Quels conseils de cybersécurité pour les Français de l’étranger, en première ligne ? Veille de veille(s) Le bulletin d’actualité du 20 avril du CERT-FR, un retour sur « les vulnérabilités significatives de la semaine passée pour souligner leurs criticités » Vulnérabilités : les 12 alertes critiques du 19 avril 2026. « L’hebdo » cybersécurité de Marc BARBEZAT actualisé tous les jours La Veille cyber hebdomadaire N.592 est en ligne, un retour sur la semaine du 13 au 19 avril 2026, sans oublier son extrait dédié intelligence artificielle RadioCSIRT : le podcast cybersécurité quotidien de Marc-Frédéric GOMEZ La protection des données personnelles – RGPD / GDPR le règlement européen et plus … Revoir le webinaire – Élections municipales 2026 : quelles sont les nouvelles règles de ciblage électoral ? La CNIL vous propose … Le bulletin d’information 119 du Contrôleur européen de la protection des données est en ligne (en) RGPD & messagerie professionnelle : l’arrêt qui change tout … un post de Cyrille CARDONNE sur LinkedIn Des nouvelles du CyberFront Chronologie des fuites de données de 1998 à 2026. ZATAZ relance son musée des sites et entreprises piratés avec une frise pensée comme un outil d’alerte, de mémoire et de lecture immédiate du risque cyber Ransomware : une économie qui change d’échelle Ransomware : derrière certaines cyberattaques, l’ombre de Moscou Sur le dark web, une identité complète vaut à peine 35 dollars Cyber attaque : signalement cyber obligatoire en quatre heures, c’est la réglementation nigérienne qui l’impose Cyberattaque : comment des hackers volent le fret routier américain. Ils piratent des transporteurs et volent des cargaisons entières Le Canada se trouve à un moment charnière de la lutte contre la criminalité financière L’éducation nationale, une cible vulnérable face aux cyberattaques, accès abonnés LeMonde L’Agence nationale des titres sécurisés a été visée par une attaque informatique, des données potentiellement « divulguées », annonce le ministère de l’Intérieur Fuite de données après un « incident de sécurité » visant le portail de l’Agence nationale des titres sécurisés (ANTS) Piratage ANTS (France Titres) : quelles données personnelles ont fuité ? Cybersécurité : L’Agence nationale des titres sécurisés (ANTS), qui gère la délivrance des cartes d’identité, passeports et permis de conduire, a été victime d’une fuite de données Incident de sécurité à l’ANTS : Ce que les entreprises et les usagers doivent savoir L’ANTS piratée à cause d’une faille basique et 19 millions de Français en font les frais, une fois de plus ! Incident de sécurité relatif au portail ants.gouv.fr, le communiqué de presse du ministère de l’intérieur Communication sur la fuite présumée de données d’état civil, le communiqué de l’ANTS Au Muséum national d’histoire naturelle, 7 000 factures en retard neuf mois après une cyberattaque, accès abonnés LeMonde Matière à réflexions « Cyberconflits » ou pas ? Une réalité diffuse complexe à appréhender Séminaires – Conférences – Journées NIS2, RGPD : éclairages sur deux réglementations phares de la sécurité numérique, une Matinale du CyberCercle Auvergne-Rhône-Alpes le 23 avril à Lyon Intelligence artificielle, sécurité et plus … IA au service de la sécurité … ou pas Le modèle Mythos d’Anthropic déclenche une réorganisation d’urgence de la cybersécurité mondiale Yoshua Bengio sonne l’alarme sur Mythos, l’IA et la menace d’une cybersécurité hors de contrôle Agents IA: les experts en cybersécurité alertent sur des risques croissants AI Index Report 2026 de Stanford : L’IA accélère, mais les garde-fous peinent à suivre (voir aussi la lettre de veille du 19 avril) Les incidents impliquant des agents IA sont désormais monnaie courante selon une étude de la Cloud Security Alliance (en) Les agents d’IA sont à l’origine d’incidents de cybersécurité dans deux tiers des entreprises La NSA utilise en secret Mythos Preview, le modèle le plus puissant d’Anthropic, l’entreprise officiellement bannie par le Pentagone qui est censée représenter un « risque pour la sécurité nationale » (la fin de l’article est réservée aux abonnés) L’Ukraine s’apprête à remplacer ses soldats de première ligne par 25 000 robots terrestres sans pilote, pour faire passer entièrement la logistique de première ligne à des systèmes robotiques Une faille exploitée dans Nginx expose des serveurs MCP Piratage chez Vercel via un outil d’IA : des données potentiellement mises en vente Vercel piraté via un outil IA tiers qui avait les clés du royaume Victime d’une intrusion, Vercel évoque un vol d’identifiants via un outil IA tierce partie Des données de Vercel compromises par une application IA tierce Vercel victime d’une intrusion via une attaque de la chaîne d’approvisionnement par une IA contextuelle (en) Des intrus assistés par l’IA ont pris le contrôle de Vercel via une violation du protocole OAuth et le vol d’un compte d’employé (en) Interrogations / Perspectives / Prospectives « C’est comme donner les plans d’une chambre forte » : pourquoi l’IA a poussé cette entreprise à abandonner l’open source En automatisant les tâches, l’IA menace plusieurs métiers (voir aussi les lettres de veille du 24 mars et du 2 avril) Pour OpenAI, 18 % des métiers présentent « un risque élevé d’automatisation à court terme » Un cadre de transition pour les emplois dans le domaine de l’IA. Cartographie de l’impact à court terme de l’IA sur l’emploi, l’étude d’OpenAI [pdf] Plus de peur que de mal… IA et automatisation ne signifieraient pas forcément « perte d’emploi » humain ! Un post de Françoise HALPER sur LinkedIn Intelligence artificielle : plus d’un emploi sur deux transformé d’ici trois ans (en) Plus on délègue à l’IA, moins on sait faire sans elle : le paradoxe de l’augmentation cognitive qui finit par amputer la cognition qu’elle prétendait amplifier, selon des études (la fin de l’article est réservée aux abonnés) Information Panne ChatGPT, Gemini et Claude : pourquoi les IA ne fonctionnent plus ? La demande en compétence agentique bondit de 60% en France 10 Bits : La liste critique de l’actualité des données du 4 au 10 avril (en) 10 Bits : La liste critique de l’actualité des données du 11 au 17 avril (en) Santé ZD Tech : Raisonnement mirage, pourquoi GPT-5 et Gemini 3 Pro inventent des diagnostics médicaux, à écouter dans le podcast « 3 minutes pour comprendre » Recherche, développement et application IA agentique : comment guider l’avènement des citizen developers Avec Claude Design, Anthropic veut tuer PowerPoint, InDesign et Figma Claude Design : Le nouveau séisme d’Anthropic qui fait trembler les géants du design Entreprises – Économie – Business Les services, nouvel eldorado de l’IA La moitié des salariés américains utilisent désormais l’IA au travail – et y consacrent près de 8 heures par semaine 23 avril 2026. Cycle de vie du développement, de l’intégration et du déploiement logiciel … l’ANSSI publie une étude du marché européen – Enfin, ça y est ! Les données de santé des français ne seront plus hébergées par Microsoft. La plateforme Health Data Hub change d’hébergeur pour l’entreprise française Scaleway – Des acteurs publics (ministères, police …) des infrastructures sportives et culturelles, des entreprises du secteur privé …, l’auteur de multiples cyberattaques récentes a été arrêté. A noter que la fuite de données de l’ANTS ; l’Agence nationale des titres (mal) sécurisés, ce n’est pas lui. – A l’origine de la fuite de données de l’ANTS, peut-être bien un défaut de configuration messagerie … A(ré)écouter – A (re)voir Cybersécurité et réglementation, frères ennemis ou alliés ? Une table ronde RiskIntel Media animée par Yasmine DOUDO Les attaquants ne piratent plus, ils se connectent : l’explosion des secrets exposés, dans le podcast « InCyber » Informations Lien armées-nation : le Commandement de la cyberdéfense rencontre les étudiants de la Sorbonne La DGSI met en garde les entreprises contre les applications et logiciels étrangers (voir aussi la lettre de veille du 21 avril) Management de la sécurité de l’Information IA et cybersécurité : anticiper aujourd’hui pour maîtriser demain, présentation de la note du Conseil de l’IA et du numérique publiée ce jour IA et cybersécurité : anticiper aujourd’hui pour maîtriser demain [pdf] Cybersécurité : face aux bouleversements de l’IA, un appel à « ne pas céder à la panique », accès abonnés LeMonde Dossier : 2026, l’année de tous les risques, un dossier LeMondeInformatique Après le chiffrement du trafic, la prochaine bataille se jouera-t-elle sur la vérification anonyme ? RSSI : 7 red flag qui doivent vous faire refuser un poste, un article JDN accessible gratuitement sous réserve d’inscription La cybersécurité est avant tout une affaire de gouvernance Cybersécurité : tout ce que les attaquants savent déjà sur votre entreprise S-SDLC et DevSecOps en Europe : Enjeux actuels et perspectives d’avenir. La sécurisation du cycle de développement logiciel n’est plus une option : c’est un enjeu stratégique ! Une nouvelle publication de l’ANSSI Étude de marché : S-SDLC / DEVSECOPS. Quels sont les défis actuels et futurs du marché européen ? La sécurisation du cycle de développement logiciel est un enjeu stratégique … un post de l’Agence sur LinkedIn DevSecOps européen : bien outillé, mais encore dominé Le mythe de la sauvegarde qui met les entreprises en danger (en) Et puis, dans la vie personnelle comme dans la vie professionnelle Fuite de données à l’ANTS : Pourquoi faut-il particulièrement se méfier en mai des cyberattaques ? Cyberattaque de l’ANTS : que faire si je suis victime d’une usurpation d’identité ? Cyberattaque massive de l’ANTS : ce qu’il faut savoir si vous êtes concernés (voir également la rubrique « Des nouvelles du CyberFront ») Veille de veille(s) La newsletter hebdomadaire Threat Landscape Intrinsec du 23 avril 2026 La protection des données personnelles – RGPD / GDPR le règlement européen et plus … Health Data Hub : Scaleway succède à Microsoft pour bâtir le sanctuaire des données de santé françaises Données de santé : le Health Data Hub quitte Microsoft Azure pour Scaleway Scaleway remporte l’hébergement des données de santé à la place de Microsoft Lignes directrices pour la recherche scientifique et certification : les derniers documents adoptés par le CEPD, le Comité européen de la protection des données Les problématiques des (r)évolutions numériques en cours Souveraineté numérique : l’Europe peut-elle s’affranchir des États-Unis ? L’automatisation alimente l’IA : le moteur caché derrière des analyses intelligentes Des nouvelles du CyberFront La guerre dans le champ électromagnétique : un enjeu stratégique invisible mais déterminant, le communiqué de presse du ComCyber, le Commandement de la cyberdéfense Des frissons et un tremplin : comment l’armée de Terre séduit la Gen Z de la cybersécurité Ce malware Android retourne votre reconnaissance faciale contre vous pour vider vos comptes bancaires Des données patients dérobées aux espaces numériques régionaux de santé en 2025 ressurgissent sur le « dark web », un article accessible gratuitement sur simple inscription sur le site TICSanté Cyberattaque en Iran : pourquoi les routeurs américains tombent en panne sans internet. Des équipements réseau iraniens tombent en panne malgré le blackout internet : voici les quatre hypothèses de Téhéran Des médias iraniens allèguent que les USA ont fait usage de portes dérobées dans des équipements réseau de fabrication américaine pour entraver les frappes militaires de l’Iran lors de moments critiques Londres. Métro : 10 millions de profils exposés après le piratage Un négociateur de rançongiciels plaide coupable dans l’affaire BlackCat (en) Un hackeur interpellé en Vendée après plusieurs cyberattaques visant notamment des fédérations sportives Angel Batista et Hexdex, le piège se referme ? HexDex interpellé, enquête ouverte en France Cyberattaques : le hacker surnommé “HexDex” est placé en garde à vue Arrestation de HexDex, pirate français spécialiste du vol de bases de données, l’analyse de Valéry RIEß-MARCHIVE Permis, CNI, passeports : vol de données après la cyberattaque de l’ANTS (voir aussi la lettre de veille du 21 avril) Incident de sécurité relatif au portail ants.gouv.fr : point d’étape du 21 avril 2026, le communiqué de presse du ministère de l’intérieur La fuite de données à l’ANTS, nouvelle illustration des failles de sécurité des services informatiques de l’État, accès abonnés LeMonde Fuite de données sur le portail de l’ANTS : près de 12 millions de comptes concernés, annonce le ministère de l’Intérieur La fuite ANTS, un leak bidon ? Derrière l’annonce d’un vol massif de données ANTS : Le « pirate » Breach3d s’explique … L’ANTS vient d’être piratée : entre 11 et 19 millions de Français concernés. Le hacker lui-même a qualifiée la faille utilisée de « vraiment stupide » … un post de Samuel KOHEN sur LinkedIn Pourquoi le piratage de France Titres (ANTS) aurait pu être évité d’après un spécialiste L’ANTS confirme un incident cyber : une configuration DMARC inactive depuis au moins 2019 Modifier un chiffre dans une URL pour accéder aux données de 19 millions de Français : le portail de l’ANTS cède face à une vulnérabilité basique, votre nom, prénom, date de naissance sont peut-être en vente Une faille sur France Titres (ANTS) expose des logs serveur et dumps mémoire accessibles en ligne, une nouvelle faille potentielle signalée par FrenchBreaches Matière à réflexions Fuite ANTS : l’État doit nous protéger et non nous exposer, une chronique de Yasmine DOUADIs Analyse coûts-avantages-risques de la R&D en cybersécurité, une étude parue dans le Journal de la cybersécurité d’Oxford University Press (en) Au Moyen-Orient, la guerre se joue aussi sur les écrans : « L’enjeu premier et final, c’est le contrôle du récit », une interview du commandant Samuel HENRY, spécialiste de la guerre informationnelle Études, enquêtes et référentiels Évaluez vos capacités et votre maturité en matière de cybersécurité nationale à l’aide du cadre ENISA mis à jour (en) L’ENISA met à jour le NCAF 2.0 pour aider les gouvernements à mesurer et combler les lacunes en matière de cybersécurité, et à promouvoir l’évaluation comparative de la maturité en cybersécurité (en) Intelligence artificielle, sécurité et plus … IA au service de la sécurité … ou pas Le gouvernement britannique alerte sur les risques cyber des nouveaux modèles d’IA Cybersécurité : Londres alerte sur les risques liés aux nouveaux modèles d’IA Conserver un avantage défensif à l’ère des cyber-capacités d’IA de pointe (en) Intelligence artificielle : « zero day » after Sans une cybergouvernance solide, ce potentiel peut rapidement se transformer en risque Agent Skills et IA autonome, le nouveau défi cybersécurité Mythos, IA et cybersécurité : la fin du mythe de l’exclusivité La plupart des entreprises sont incapables de contrer les menaces posées par les agents d’IA de niveau 3, selon une enquête de VentureBeat (en) IA et automatisation : gains opérationnels et zones de vigilance La plupart des « SOC IA » se contentent d’un triage plus rapide. Ce n’est pas suffisant (en) Ils traquent les modèles d’IA cachés, tombent sur Claude Mythos et n’en font pratiquement rien. En tout cas, c’est ce qu’ils disent Fuite Claude Mythos : comment des utilisateurs ont accédé à l’IA d’Anthropic Anthropic enquête après un accès non autorisé à son modèle d’IA Mythos « Les jours des zero-days sont comptés » : Claude Mythos a donné des sueurs froides à Firefox, et ça a payé Les zero-days sont comptés. Firefox 150 intègre des correctifs pour 271 vulnérabilités découvertes par Claude Mythos Preview . Le communiqué de presse (en) L’IA peut-elle attaquer le cloud ? Leçons tirées de la construction d’un système multi-agents offensif autonome dans le cloud, une étude Unit42 Interrogations / Perspectives / Prospectives Cyber : Google investit 32 milliards de dollars dans une cyberarmée d’agents IA Une start-up veut confier la vérité à un « tribunal IA » chargé de juger les journalistes dans « Bientôt chez vous » sur France Info Information Meta transforme l’activité de ses salariés en « carburant » pour ses agents IA IA & Cybersécurité : les 11 actus clés du 22 avril 2026 de Marc BARBEZAT Recherche, développement et application Avec ChatGPT Images 2.0, OpenAI déclare la guerre à Google et veut vous faire oublier Nano Banana Entreprises – Économie – Business IA agentique : les nouvelles compétences que les entreprises recherchent (à rapprocher de La demande en compétence agentique bondit de 60% en France) Ces entreprises forment leurs employés à l’IA : voici comment elles s’y prennent Le développement à grande échelle de l’IA agentique nécessite des données solides : 4 étapes à suivre en premier lieu IA : cinq signaux d’alerte révélateurs des limites d’une infrastructure 26 avril 2026. Les données médicales de 500 000 patients britanniques mises en vente sur Alibaba avant d’être promptement enlevées – Se défendre contre les réseaux clandestins d’appareils compromis liés à la Chine, une alerte des agences internationales de cybersécurité – Cette fois, c’est Parcoursup qui a été touché, plus exactement 705 000 candidats des sessions 2023 et 2025 inscrits en Occitanie. Noms, prénoms, nationalité, date de naissance, adresses, téléphones dérobés… l’ordinaire, quoi ! Les magasins U aussi avec le N . de carte de fidélité en plus … A(ré)écouter – A (re)voir Sommes-nous encore en sécurité sur le net ? Vidéo d’un « Cyber talk » RiskIntel avec Eric ANTIBI Informations Affaire du porte-avions Charles-de-Gaulle : le chef d’Etat-major calme le jeu La Dinum précise sa feuille de route de bascule sur Linux Passage de Windows à Linux : pourquoi la France s’apprête à tourner le dos aux outils numériques américains Management de la sécurité de l’Information RSSI et DPO : complémentarité ou schizophrénie des fonctions ? Une analyse de Cédric CARTAU DORA et résilience opérationnelle : la gestion des identifiants comme contrôle des risques financiers (en) ISO 27001-NIST CSF- IEC 62443 … Penser qu’un seul référentiel suffit en cybersécurité OT est déjà une approximation. Mais croire qu’ils jouent tous le même rôle en est une autre … un post de Ndeye Adama DRAME sur LinkedIn Planifier la reprise d’activité après un incident : les 11 étapes clés Les réinitialisations régulières de mots de passe ne sont pas aussi sûres qu’on le croit (en) Des pirates obtiennent via Teams un accès distant aux postes de salariés La persévérance plutôt que l’impact : les leçons tirées du front ukrainien de la cyberguerre (en) Et puis, dans la vie personnelle comme dans la vie professionnelle Des fermes de cartes SIM vous inondent de SMS frauduleux – et comment se protéger Arnaque Leboncoin en 2026 : comment un vendeur a perdu 1550 euros Veille de veille(s) Sur LinkedIn, la lettre de veille hebdomadaire de Francis BRUCKMANN, Administrateur de l’ARCSI, concernant la semaine 17 (du 20 au 26 avril) et rapportant les faits marquants en sécurité et technologies de l’Information Cyberhebdo du 24 avril 2026 : mauvaise semaine pour le secteur public, le Cyberhebdo LeMagIT RadioCSIRT : le podcast cybersécurité quotidien de Marc-Frédéric GOMEZ Mimétisme, carte postale et jeux vidéos, la cyber-revue de la semaine de Rayna STAMBOLIYSKA La protection des données personnelles – RGPD / GDPR le règlement européen et plus … Vote par correspondance électronique : la CNIL met à jour sa recommandation Depuis le RGPD, les fuites de données explosent-elles vraiment ? Adieu Microsoft et bonjour Scaleway pour l’hébergement des données de santé des Français (voir aussi la lettre de veille du 23 avril) La Plateforme des données de santé fait le choix du cloud souverain avec Scaleway « Une alternative européenne crédible et compétitive existe »: le gouvernement choisit le Français Scaleway pour remplacer Microsoft et héberger nos données de santé La France retire ses dossiers médicaux à Microsoft pour les confier au groupe Iliad Les problématiques des (r)évolutions numériques en cours Des nouvelles du CyberFront DÉCRYPTAGE. Piratages, fuites de données : pourquoi la France est autant ciblée Comment les attaquants se cachent en utilisant la virtualisation Les agences de cybersécurité signalent l’utilisation de réseaux clandestins par des acteurs liés à la Chine à des fins d’espionnage et d’opérations offensives (en) Défense contre les réseaux clandestins d’appareils compromis liés à la Chine. Changement généralisé des tactiques, techniques et procédures (TTP) des cybermalveillants liés à la Chine, analyse et recommandations du NCSC, le Centre national de cybersécurité britannique (en) Le paysage des cybermenaces en Chine évolue rapidement (en) La Chronologie des cyberattaques du 1er au 15 avril 2026 d’Hackmageddon (en) Le Cambodge pressé par la Chine d’ »éradiquer totalement » les centres de cyberfraude TheGentlemen, une enseigne de ransomware aux débuts fracassants Kyber, ce ransomware qui teste le chiffrement post-quantique sur Windows Le gang de ransomware Kyber joue avec le chiffrement post-quantique sur Windows Double menace du ransomware Kyber : explication des attaques contre Windows et ESXi, l’analyse technique de Rapid7 (en) En Russie, Internet est en train de disparaître Royaume-Uni : les données médicales de 500 000 personnes proposées à la vente en Chine Données médicales volées de 500 000 volontaires britanniques mises en vente sur un site chinois Après avoir été téléchargées légalement par trois centres de recherches chinois, les données médicales de 500.000 Britanniques se sont retrouvées en vente sur Alibaba, une enquête est en cours En Allemagne, une cyberattaque « extrêmement préoccupante » de la messagerie Signal touche la classe politique, la Russie suspect numéro un Le jeune hacker « HexDex », soupçonné d’une vague de cyberattaques, a été mis en examen et écroué (voir aussi la lettre de veille du 23 avril) Un hackeur, surnommé « HexDex », mis en examen et écroué après plusieurs cyberattaques visant notamment des fédérations sportives « Pour gagner de l’argent, je n’ai pas de limite » : l’édifiant CV d’HexDex, le hackeur mis en examen pour avoir volé les données de millions de Français, accès abonnés LeFigaro Parcoursup victime d’une cyberattaque : les données de 705.000 anciens candidats piratées Catastrophe, cette fois, c’est Parcoursup qui se fait pirater ! 705 000 candidats concernés par une fuite de données Fuite de données chez Parcoursup : la cyberattaque est passée inaperçue pendant cinq mois Parcoursup piraté : les données de 705 000 candidats voléesLa plateforme Parcoursup a été piratée : ce que l’on sait de cette intrusion inédite Incident de sécurité affectant les données de certains candidats des sessions Parcoursup 2023 et 2025 résidant ou ayant formulé des vœux en Occitanie, le communiqué de presse du ministère Les Magasins U ont été piratés : les données des clients ont été compromises Cyberattaque chez les magasins U : pensez à changer votre mot de passe Matière à réflexions La cybersécurité est une « priorité géopolitique », pas un « problème technique » (1/3), un article de Jean-Marc MANACH, accès abonnés Next Études, enquêtes et référentiels APT, ingénierie sociale et red teaming, ce que les données 2025 de Kaspersky révèlent sur l’exposition réelle des secteurs critiques Séminaires – Conférences – Journées Rejoignez le collectif Cybermois 2026 ! Cybermois 2026. Engageons-nous ensemble pour le Cybermois ! Le message de Cybermalveillance.gouv.fr sur LinkedIn Une première compétition de cybersécurité en Alsace : malgré le retard du Grand Est dans le numérique, « on a des talents ici » Intelligence artificielle, sécurité et plus … IA au service de la sécurité … ou pas Les risques de l’IA agentique autonome vus par l’ANSSI L’hameçonnage par IA est la méthode de prédilection des cybercriminels (en) Les mauvais souvenirs hantent encore les agents IA Google Cloud dévoile sa nouvelle stratégie de cybersécurité face à l’essor de l’IA “Combattre l’IA par l’IA” : Face à l’explosion des menaces, Google Cloud mise sur l’IA agentique pour transformer les métiers de la cybersécurité Comment Claude Desktop installe une porte dérobée dans vos navigateurs sans vous le dire Claude Desktop : Anthropic, champion autoproclamé de l’IA responsable, préinstalle discrètement un accès à vos sessions navigateur, y compris pour des logiciels que vous n’avez pas encore installés, la fin de l’article est réservé aux abonnés De l’Australie à l’Europe, en passant par les États-Unis, comment Anthropic est devenu, avec son tout nouveau modèle frontière, la star du moment de la cybersécurité sur BFM Tech Mythos: l’intelligence artificielle qui fait trembler la finance mondial dans « Aujourd’hui l’économie » sur RFI Cybersécurité : Mythos, l’intelligence artificielle d’Anthropic qui protège… et inquiète Souveraineté numérique et Claude Mythos : Un appel à l’action et nos propositions pour la France, l’Europe et l’open source IA & cybersécurité : un basculement imminent ? … Un post du CLUSIF Un agent IA chinois a trouvé près de 1 000 failles inédites, dont certaines dans Microsoft Office Interrogations / Perspectives / Prospectives IA Secure : sommes-nous vraiment impuissants face à la menace ? Les agents IA vont-ils changer la nature même du travail en entreprise ? C’est la vision de Google avec Workspace Intelligence et Gemini Enterprise Information L’IA au sommaire de l’émission de Frédéric SIMOTTEL sur BFM Tech&Co le 21 avril La note qui annonce une nouvelle phase dans la guerre de l’IA L’IA fait passer les jumeaux numériques dans une autre dimension 10 Bits : La liste critique de l’actualité des données du 18 au 24 avril (en) Enseignement L’intelligence artificielle de pointe, une information du Centre canadien pour la cybersécurité Anthropic offre (discrètement) 13 formations gratuites, un post de Clément PREDO sur LinkedIn Recherche, développement et application Les États-Unis accusent la Chine de voler leur IA « à l’échelle industrielle » via la technique de distillation : Pékin dénonce une « calomnie » et DeepSeek, visé implicitement, publie son modèle V4, la fin de l’article est réservée aux abonnés L’entreprise chinoise DeepSeek lance un nouveau modèle d’intelligence artificielle 7 fois moins cher que Claude Opus 4.7 : la Chine dégaine DeepSeek-V4, un modèle open source conçu pour vous détourner des États-Unis OpenAI dévoile GPT-5.5 et veut faire une remontada historique face à Claude et Gemini OpenAI dévoile GPT-5.5 et veut faire une remontada historique face à Claude et Gemini OpenAI dégaine son nouveau modèle GPT-5.5 et lance un défie à Anthropic GPT-5.5 : les promesses d’OpenAI contredites par les premiers retours Google a une arme secrète pour gagner la guerre de l’IA : les TPU 8t et TPU 8i Entreprises – Économie – Business Une part des bénéfices de l’IA effacée par la correction d’erreurs Cette sélection, parfaitement partielle et partiale, de sujets proposés irrégulièrement à votre attention n’est possible que par le travail de veille et de partage réalisé en amont par différentes sources que je remercie. A votre disposition pour recueillir vos observations, suggestions, commentaires et … demandes de suspension d’envoi, bien évidemment. Avec mes cordiales salutations. Lionel Guillet Une précision – Les recherches ciblées sur les lettres de veille archivées sont désormais possibles par l’intermédiaire d’un widget sur la page d’accueil du site https://veillecyberland.wordpress.com/ Un mot-clé, sa validation, et le système vous affiche la liste des lettres qui le contiennent.Il suffit alors de cliquer sur le lien hypertexte de chacune des lettres pour les ouvrir et lancer une recherche par CTRL+F sur leur contenu. La transaction manque d’élégance, mais elle est efficace. Elle peut vous être utile pour une étude, pour préparer une intervention, une présentation, etc. À votre disposition pour recueillir vos observations, suggestions et commentaires sur cette information guillet.lionel@gmail.com
- Analyse de marchés publics : découvrez l’outil Odianapar Stephannie R. le 30 avril 2026 à 12h30
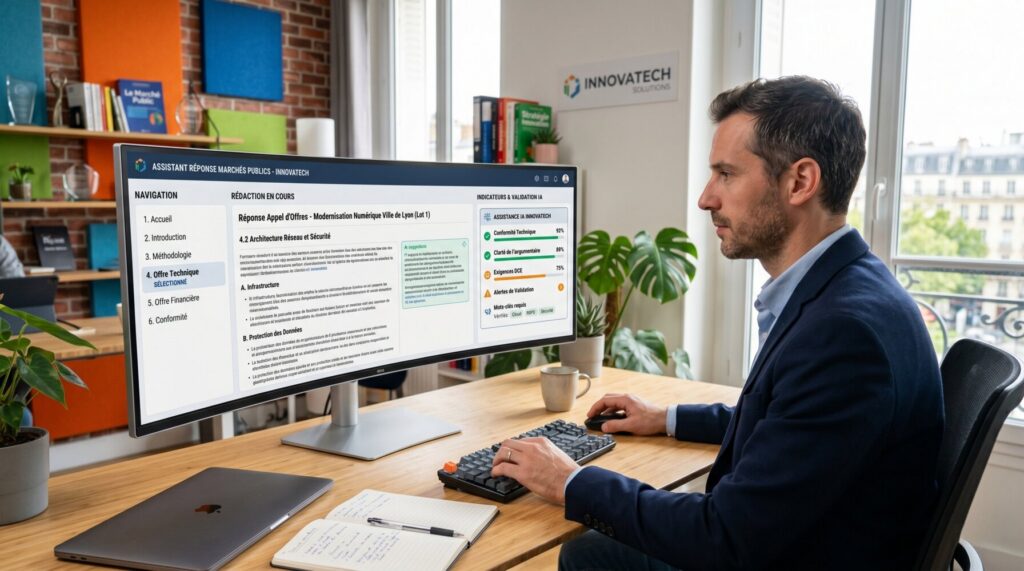
Le cabinet lyonnais Odialis bouscule le secteur des marchés publics avec Odiana. C’est un outil d’intelligence artificielle pensé pour les TPE et PME. Cette plateforme souveraine transforme des dossiers administratifs complexes en données exploitables pour les dirigeants. L’accès aux contrats d’État reste un défi technique pour de nombreux patrons de petites entreprises. Pour lever ces barrières, l’expert lyonnais Odialis déploie Odiana. Il s’agit d’une solution logicielle capable de scanner les appels d’offres en un clin d’œil. L’idée consiste à extraire immédiatement les points de vigilance et les obligations de chaque dossier pour éviter les mauvaises surprises. Une alliance entre algorithme et savoir-faire métier Le logiciel ne se limite pas à un simple résumé textuel. Il s’appuie sur une base de seize années d’expérience terrain pour orienter la stratégie commerciale des utilisateurs. Selon Olivier Demilly, dirigeant de la structure, la technologie n’apporte une réelle plus-value que si elle s’accompagne d’une vision métier concrète. Dans la pratique, l’outil propose un appui pour trancher sur l’intérêt de postuler, ce fameux arbitrage « Go / No Go » souvent chronophage. La plateforme accompagne ensuite la construction du mémoire technique. C’est important pour booster la qualité des réponses et limiter le risque d’éviction administrative. La souveraineté numérique comme socle technique Côté infrastructure, l’accent est mis sur la protection des données sensibles. Odiana repose sur une architecture 100 % française et garantit un hébergement local et une conformité totale au RGPD. Avec les modèles de langage de Mistral AI, l’entreprise s’affranchit des législations étrangères pour offrir une sécurité maximale aux acteurs économiques. Cette innovation a vu le jour grâce à un écosystème solide qui inclut Bpifrance et des partenaires industriels comme La Poste. Proposé dès 49 euros/mois, le service cible directement les structures qui souhaitent automatiser leur veille et leurs candidatures sans exploser leur budget. Article basé sur un communiqué de presse reçu par la rédaction. Cet article Analyse de marchés publics : découvrez l’outil Odiana a été publié sur LEBIGDATA.FR.
- Veille Cyber N593 – 27 avril 2026par veillecybertb le 30 avril 2026 à 10h05
Veille hebdomadaire du 26 avril 2026 CyberStratégie /CyberDéfense / CyberSécurité – Protection des données / RGPD – Intelligence artificielle … Lettre Cyber 593 L’actualité cyber du 20 au 26 avril 2026 …… faits, chroniques et opinions, référentiels, séquences audio, séquences vidéo … selon vos centres d’intérêt, personnels ou professionnels, je vous laisse découvrir l’actualité de la semaine, dans ces domaines essentiels que sont … la CyberStratégie, la CyberSécurité, la protection des données personnelles et l’intelligence artificielle … sans prétention à l’exhaustivité et avec beaucoup de subjectivité, inévitable, bien évidemment. Une bonne semaine à vous. Sans oublier que je reste à l’écoute de vos commentaires et de vos observations guillet.lionel@gmail.com Ce qui a retenu mon attention dans l’actualité de cette semaine 21 avril 2026. Toutes les vidéos des auditions de la Commission d’enquête de l’Assemblée nationale sur les dépendances numériques sont en ligne – L’Agence Nationale des Titres Sécurisés … pas tant que cela, nouvelle fuite massive de données à caractère personnel gérées par un service public, l’ANTS touchée par une cyberattaque – Fuite de données chez Vercel, une plateforme de développement cloud. A l’origine, une application d’IA tierce … A(ré)écouter – A (re)voir Cyberattaques : les collectivités territoriales, particulièrement ciblées, doivent apprendre à résister dans la chronique “Nouveau monde” de Nicolas ARPAGIAN sur FranceInfo (voir aussi la lettre de veille du 19 avril) Toutes les vidéos des auditions de la Commission d’enquête de l’Assemblée nationale sur les dépendances structurelles et les vulnérabilités dans le secteur numérique et les risques pour l’indépendance de la France sont ici … Des ministères cherchent des alternatives aux éditeurs logiciels US Le rapport M-Trends 2026 de Mandiant analysé au micro de l’équipe NoLimitSecu cette semaine avec David GROUT Histoire de la Cyber Française – FSSI, Matignon & Santé avec Philippe Loudenot, une vidéo de son interview Informations Négationnisme, deepfakes, usurpation d’identité… On vous résume les accusations qui visent le réseau X et pour lesquelles Elon Musk est convoqué devant la justice française Affaire X : le bras de fer entre Elon Musk et la justice français entre dans sa phase critique La Commission européenne met 180 millions sur le cloud souverain, voici qui sont les gagnants Loi SREN : le décret attendu qui redéfinit les règles du cloud pour les administrations Management de la sécurité de l’Information Cybersécurité : quand la menace oblige à repenser le périmètre de la sécurité Identités sous pression : quand l’IA et la cryptographie redessinent la surface d’attaque Les réseaux sociaux professionnels, terrain de chasse de nombreux services de renseignement, un livret de sensibilisation de la DGSI, la Direction Générale de la Sécurité Intérieure Sécurité économique : Pourquoi la DGSI recommande aux entreprises de bannir certaines solutions SaaS étrangères (voir aussi la lettre de veille du 19 avril sur le flas ingérence de la DGSI) L’ensemble des interviews du Global Security Mag dans le contexte du Forum InCyber qui a eu lieu du 31 mars au 2 avril ici … Cyberassurance : les conflits de 2026 durcissent les clauses de guerre SOC : comment améliorer l’expérience des analystes et pourquoi c’est important Fuite de données ou violation de données ? Votre stockage en cloud est-il compatible avec l’IA ? Cybersécurité OT et IA, 5 stratégies contre les cybermenaces L’identité est le nouveau périmètre : surmonter les points faibles d’Active Directory Comment la réduction des activités de gestion des CVE par le NIST affecte les équipes de cybersécurité (en) (voir aussi la lettre de veille du 19 avril) La fonction Recall dans Windows reste toujours vulnérable Et puis, dans la vie personnelle comme dans la vie professionnelle Quels conseils de cybersécurité pour les Français de l’étranger, en première ligne ? Veille de veille(s) Le bulletin d’actualité du 20 avril du CERT-FR, un retour sur “les vulnérabilités significatives de la semaine passée pour souligner leurs criticités” Vulnérabilités : les 12 alertes critiques du 19 avril 2026. “L’hebdo” cybersécurité de Marc BARBEZAT actualisé tous les jours La Veille cyber hebdomadaire N.592 est en ligne, un retour sur la semaine du 13 au 19 avril 2026, sans oublier son extrait dédié intelligence artificielle RadioCSIRT : le podcast cybersécurité quotidien de Marc-Frédéric GOMEZ La protection des données personnelles – RGPD / GDPR le règlement européen et plus … Revoir le webinaire – Élections municipales 2026 : quelles sont les nouvelles règles de ciblage électoral ? La CNIL vous propose … Le bulletin d’information 119 du Contrôleur européen de la protection des données est en ligne (en) RGPD & messagerie professionnelle : l’arrêt qui change tout … un post de Cyrille CARDONNE sur LinkedIn Des nouvelles du CyberFront Chronologie des fuites de données de 1998 à 2026. ZATAZ relance son musée des sites et entreprises piratés avec une frise pensée comme un outil d’alerte, de mémoire et de lecture immédiate du risque cyber Ransomware : une économie qui change d’échelle Ransomware : derrière certaines cyberattaques, l’ombre de Moscou Sur le dark web, une identité complète vaut à peine 35 dollars Cyber attaque : signalement cyber obligatoire en quatre heures, c’est la réglementation nigérienne qui l’impose Cyberattaque : comment des hackers volent le fret routier américain. Ils piratent des transporteurs et volent des cargaisons entières Le Canada se trouve à un moment charnière de la lutte contre la criminalité financière L’éducation nationale, une cible vulnérable face aux cyberattaques, accès abonnés LeMonde L’Agence nationale des titres sécurisés a été visée par une attaque informatique, des données potentiellement “divulguées”, annonce le ministère de l’Intérieur Fuite de données après un “incident de sécurité” visant le portail de l’Agence nationale des titres sécurisés (ANTS) Piratage ANTS (France Titres) : quelles données personnelles ont fuité ? Cybersécurité : L’Agence nationale des titres sécurisés (ANTS), qui gère la délivrance des cartes d’identité, passeports et permis de conduire, a été victime d’une fuite de données Incident de sécurité à l’ANTS : Ce que les entreprises et les usagers doivent savoir L’ANTS piratée à cause d’une faille basique et 19 millions de Français en font les frais, une fois de plus ! Incident de sécurité relatif au portail ants.gouv.fr, le communiqué de presse du ministère de l’intérieur Communication sur la fuite présumée de données d’état civil, le communiqué de l’ANTS Au Muséum national d’histoire naturelle, 7 000 factures en retard neuf mois après une cyberattaque, accès abonnés LeMonde Matière à réflexions “Cyberconflits” ou pas ? Une réalité diffuse complexe à appréhender Séminaires – Conférences – Journées NIS2, RGPD : éclairages sur deux réglementations phares de la sécurité numérique, une Matinale du CyberCercle Auvergne-Rhône-Alpes le 23 avril à Lyon Intelligence artificielle, sécurité et plus … IA au service de la sécurité … ou pas Le modèle Mythos d’Anthropic déclenche une réorganisation d’urgence de la cybersécurité mondiale Yoshua Bengio sonne l’alarme sur Mythos, l’IA et la menace d’une cybersécurité hors de contrôle Agents IA: les experts en cybersécurité alertent sur des risques croissants AI Index Report 2026 de Stanford : L’IA accélère, mais les garde-fous peinent à suivre (voir aussi la lettre de veille du 19 avril) Les incidents impliquant des agents IA sont désormais monnaie courante selon une étude de la Cloud Security Alliance (en) Les agents d’IA sont à l’origine d’incidents de cybersécurité dans deux tiers des entreprises La NSA utilise en secret Mythos Preview, le modèle le plus puissant d’Anthropic, l’entreprise officiellement bannie par le Pentagone qui est censée représenter un “risque pour la sécurité nationale” (la fin de l’article est réservée aux abonnés) L’Ukraine s’apprête à remplacer ses soldats de première ligne par 25 000 robots terrestres sans pilote, pour faire passer entièrement la logistique de première ligne à des systèmes robotiques Une faille exploitée dans Nginx expose des serveurs MCP Piratage chez Vercel via un outil d’IA : des données potentiellement mises en vente Vercel piraté via un outil IA tiers qui avait les clés du royaume Victime d’une intrusion, Vercel évoque un vol d’identifiants via un outil IA tierce partie Des données de Vercel compromises par une application IA tierce Vercel victime d’une intrusion via une attaque de la chaîne d’approvisionnement par une IA contextuelle (en) Des intrus assistés par l’IA ont pris le contrôle de Vercel via une violation du protocole OAuth et le vol d’un compte d’employé (en) Interrogations / Perspectives / Prospectives “C’est comme donner les plans d’une chambre forte” : pourquoi l’IA a poussé cette entreprise à abandonner l’open source En automatisant les tâches, l’IA menace plusieurs métiers (voir aussi les lettres de veille du 24 mars et du 2 avril) Pour OpenAI, 18 % des métiers présentent “un risque élevé d’automatisation à court terme” Un cadre de transition pour les emplois dans le domaine de l’IA. Cartographie de l’impact à court terme de l’IA sur l’emploi, l’étude d’OpenAI [pdf] Plus de peur que de mal… IA et automatisation ne signifieraient pas forcément “perte d’emploi” humain ! Un post de Françoise HALPER sur LinkedIn Intelligence artificielle : plus d’un emploi sur deux transformé d’ici trois ans (en) Plus on délègue à l’IA, moins on sait faire sans elle : le paradoxe de l’augmentation cognitive qui finit par amputer la cognition qu’elle prétendait amplifier, selon des études (la fin de l’article est réservée aux abonnés) Information Panne ChatGPT, Gemini et Claude : pourquoi les IA ne fonctionnent plus ? La demande en compétence agentique bondit de 60% en France 10 Bits : La liste critique de l’actualité des données du 4 au 10 avril (en) 10 Bits : La liste critique de l’actualité des données du 11 au 17 avril (en) Santé ZD Tech : Raisonnement mirage, pourquoi GPT-5 et Gemini 3 Pro inventent des diagnostics médicaux, à écouter dans le podcast “3 minutes pour comprendre” Recherche, développement et application IA agentique : comment guider l’avènement des citizen developers Avec Claude Design, Anthropic veut tuer PowerPoint, InDesign et Figma Claude Design : Le nouveau séisme d’Anthropic qui fait trembler les géants du design Entreprises – Économie – Business Les services, nouvel eldorado de l’IA La moitié des salariés américains utilisent désormais l’IA au travail – et y consacrent près de 8 heures par semaine 23 avril 2026. Cycle de vie du développement, de l’intégration et du déploiement logiciel … l’ANSSI publie une étude du marché européen – Enfin, ça y est ! Les données de santé des français ne seront plus hébergées par Microsoft. La plateforme Health Data Hub change d’hébergeur pour l’entreprise française Scaleway – Des acteurs publics (ministères, police …) des infrastructures sportives et culturelles, des entreprises du secteur privé …, l’auteur de multiples cyberattaques récentes a été arrêté. A noter que la fuite de données de l’ANTS ; l’Agence nationale des titres (mal) sécurisés, ce n’est pas lui. – A l’origine de la fuite de données de l’ANTS, peut-être bien un défaut de configuration messagerie … A(ré)écouter – A (re)voir Cybersécurité et réglementation, frères ennemis ou alliés ? Une table ronde RiskIntel Media animée par Yasmine DOUDO Les attaquants ne piratent plus, ils se connectent : l’explosion des secrets exposés, dans le podcast “InCyber” Informations Lien armées-nation : le Commandement de la cyberdéfense rencontre les étudiants de la Sorbonne La DGSI met en garde les entreprises contre les applications et logiciels étrangers (voir aussi la lettre de veille du 21 avril) Management de la sécurité de l’Information IA et cybersécurité : anticiper aujourd’hui pour maîtriser demain, présentation de la note du Conseil de l’IA et du numérique publiée ce jour IA et cybersécurité : anticiper aujourd’hui pour maîtriser demain [pdf] Cybersécurité : face aux bouleversements de l’IA, un appel à “ne pas céder à la panique”, accès abonnés LeMonde Dossier : 2026, l’année de tous les risques, un dossier LeMondeInformatique Après le chiffrement du trafic, la prochaine bataille se jouera-t-elle sur la vérification anonyme ? RSSI : 7 red flag qui doivent vous faire refuser un poste, un article JDN accessible gratuitement sous réserve d’inscription La cybersécurité est avant tout une affaire de gouvernance Cybersécurité : tout ce que les attaquants savent déjà sur votre entreprise S-SDLC et DevSecOps en Europe : Enjeux actuels et perspectives d’avenir. La sécurisation du cycle de développement logiciel n’est plus une option : c’est un enjeu stratégique ! Une nouvelle publication de l’ANSSI Étude de marché : S-SDLC / DEVSECOPS. Quels sont les défis actuels et futurs du marché européen ? La sécurisation du cycle de développement logiciel est un enjeu stratégique … un post de l’Agence sur LinkedIn DevSecOps européen : bien outillé, mais encore dominé Le mythe de la sauvegarde qui met les entreprises en danger (en) Et puis, dans la vie personnelle comme dans la vie professionnelle Fuite de données à l’ANTS : Pourquoi faut-il particulièrement se méfier en mai des cyberattaques ? Cyberattaque de l’ANTS : que faire si je suis victime d’une usurpation d’identité ? Cyberattaque massive de l’ANTS : ce qu’il faut savoir si vous êtes concernés (voir également la rubrique “Des nouvelles du CyberFront”) Veille de veille(s) La newsletter hebdomadaire Threat Landscape Intrinsec du 23 avril 2026 La protection des données personnelles – RGPD / GDPR le règlement européen et plus … Health Data Hub : Scaleway succède à Microsoft pour bâtir le sanctuaire des données de santé françaises Données de santé : le Health Data Hub quitte Microsoft Azure pour Scaleway Scaleway remporte l’hébergement des données de santé à la place de Microsoft Lignes directrices pour la recherche scientifique et certification : les derniers documents adoptés par le CEPD, le Comité européen de la protection des données Les problématiques des (r)évolutions numériques en cours Souveraineté numérique : l’Europe peut-elle s’affranchir des États-Unis ? L’automatisation alimente l’IA : le moteur caché derrière des analyses intelligentes Des nouvelles du CyberFront La guerre dans le champ électromagnétique : un enjeu stratégique invisible mais déterminant, le communiqué de presse du ComCyber, le Commandement de la cyberdéfense Des frissons et un tremplin : comment l’armée de Terre séduit la Gen Z de la cybersécurité Ce malware Android retourne votre reconnaissance faciale contre vous pour vider vos comptes bancaires Des données patients dérobées aux espaces numériques régionaux de santé en 2025 ressurgissent sur le “dark web”, un article accessible gratuitement sur simple inscription sur le site TICSanté Cyberattaque en Iran : pourquoi les routeurs américains tombent en panne sans internet. Des équipements réseau iraniens tombent en panne malgré le blackout internet : voici les quatre hypothèses de Téhéran Des médias iraniens allèguent que les USA ont fait usage de portes dérobées dans des équipements réseau de fabrication américaine pour entraver les frappes militaires de l’Iran lors de moments critiques Londres. Métro : 10 millions de profils exposés après le piratage Un négociateur de rançongiciels plaide coupable dans l’affaire BlackCat (en) Un hackeur interpellé en Vendée après plusieurs cyberattaques visant notamment des fédérations sportives Angel Batista et Hexdex, le piège se referme ? HexDex interpellé, enquête ouverte en France Cyberattaques : le hacker surnommé “HexDex” est placé en garde à vue Arrestation de HexDex, pirate français spécialiste du vol de bases de données, l’analyse de Valéry RIEß-MARCHIVE Permis, CNI, passeports : vol de données après la cyberattaque de l’ANTS (voir aussi la lettre de veille du 21 avril) Incident de sécurité relatif au portail ants.gouv.fr : point d’étape du 21 avril 2026, le communiqué de presse du ministère de l’intérieur La fuite de données à l’ANTS, nouvelle illustration des failles de sécurité des services informatiques de l’État, accès abonnés LeMonde Fuite de données sur le portail de l’ANTS : près de 12 millions de comptes concernés, annonce le ministère de l’Intérieur La fuite ANTS, un leak bidon ? Derrière l’annonce d’un vol massif de données ANTS : Le “pirate” Breach3d s’explique … L’ANTS vient d’être piratée : entre 11 et 19 millions de Français concernés. Le hacker lui-même a qualifiée la faille utilisée de “vraiment stupide” … un post de Samuel KOHEN sur LinkedIn Pourquoi le piratage de France Titres (ANTS) aurait pu être évité d’après un spécialiste L’ANTS confirme un incident cyber : une configuration DMARC inactive depuis au moins 2019 Modifier un chiffre dans une URL pour accéder aux données de 19 millions de Français : le portail de l’ANTS cède face à une vulnérabilité basique, votre nom, prénom, date de naissance sont peut-être en vente Une faille sur France Titres (ANTS) expose des logs serveur et dumps mémoire accessibles en ligne, une nouvelle faille potentielle signalée par FrenchBreaches Matière à réflexions Fuite ANTS : l’État doit nous protéger et non nous exposer, une chronique de Yasmine DOUADIs Analyse coûts-avantages-risques de la R&D en cybersécurité, une étude parue dans le Journal de la cybersécurité d’Oxford University Press (en) Au Moyen-Orient, la guerre se joue aussi sur les écrans : “L’enjeu premier et final, c’est le contrôle du récit”, une interview du commandant Samuel HENRY, spécialiste de la guerre informationnelle Études, enquêtes et référentiels Évaluez vos capacités et votre maturité en matière de cybersécurité nationale à l’aide du cadre ENISA mis à jour (en) L’ENISA met à jour le NCAF 2.0 pour aider les gouvernements à mesurer et combler les lacunes en matière de cybersécurité, et à promouvoir l’évaluation comparative de la maturité en cybersécurité (en) Intelligence artificielle, sécurité et plus … IA au service de la sécurité … ou pas Le gouvernement britannique alerte sur les risques cyber des nouveaux modèles d’IA Cybersécurité : Londres alerte sur les risques liés aux nouveaux modèles d’IA Conserver un avantage défensif à l’ère des cyber-capacités d’IA de pointe (en) Intelligence artificielle : “zero day” after Sans une cybergouvernance solide, ce potentiel peut rapidement se transformer en risque Agent Skills et IA autonome, le nouveau défi cybersécurité Mythos, IA et cybersécurité : la fin du mythe de l’exclusivité La plupart des entreprises sont incapables de contrer les menaces posées par les agents d’IA de niveau 3, selon une enquête de VentureBeat (en) IA et automatisation : gains opérationnels et zones de vigilance La plupart des “SOC IA” se contentent d’un triage plus rapide. Ce n’est pas suffisant (en) Ils traquent les modèles d’IA cachés, tombent sur Claude Mythos et n’en font pratiquement rien. En tout cas, c’est ce qu’ils disent Fuite Claude Mythos : comment des utilisateurs ont accédé à l’IA d’Anthropic Anthropic enquête après un accès non autorisé à son modèle d’IA Mythos “Les jours des zero-days sont comptés” : Claude Mythos a donné des sueurs froides à Firefox, et ça a payé Les zero-days sont comptés. Firefox 150 intègre des correctifs pour 271 vulnérabilités découvertes par Claude Mythos Preview . Le communiqué de presse (en) L’IA peut-elle attaquer le cloud ? Leçons tirées de la construction d’un système multi-agents offensif autonome dans le cloud, une étude Unit42 Interrogations / Perspectives / Prospectives Cyber : Google investit 32 milliards de dollars dans une cyberarmée d’agents IA Une start-up veut confier la vérité à un “tribunal IA” chargé de juger les journalistes dans “Bientôt chez vous” sur France Info Information Meta transforme l’activité de ses salariés en “carburant” pour ses agents IA IA & Cybersécurité : les 11 actus clés du 22 avril 2026 de Marc BARBEZAT Recherche, développement et application Avec ChatGPT Images 2.0, OpenAI déclare la guerre à Google et veut vous faire oublier Nano Banana Entreprises – Économie – Business IA agentique : les nouvelles compétences que les entreprises recherchent (à rapprocher de La demande en compétence agentique bondit de 60% en France) Ces entreprises forment leurs employés à l’IA : voici comment elles s’y prennent Le développement à grande échelle de l’IA agentique nécessite des données solides : 4 étapes à suivre en premier lieu IA : cinq signaux d’alerte révélateurs des limites d’une infrastructure 26 avril 2026. Les données médicales de 500 000 patients britanniques mises en vente sur Alibaba avant d’être promptement enlevées – Se défendre contre les réseaux clandestins d’appareils compromis liés à la Chine, une alerte des agences internationales de cybersécurité – Cette fois, c’est Parcoursup qui a été touché, plus exactement 705 000 candidats des sessions 2023 et 2025 inscrits en Occitanie. Noms, prénoms, nationalité, date de naissance, adresses, téléphones dérobés… l’ordinaire, quoi ! Les magasins U aussi avec le N . de carte de fidélité en plus … A(ré)écouter – A (re)voir Sommes-nous encore en sécurité sur le net ? Vidéo d’un “Cyber talk” RiskIntel avec Eric ANTIBI Informations Affaire du porte-avions Charles-de-Gaulle : le chef d’Etat-major calme le jeu La Dinum précise sa feuille de route de bascule sur Linux Passage de Windows à Linux : pourquoi la France s’apprête à tourner le dos aux outils numériques américains Management de la sécurité de l’Information RSSI et DPO : complémentarité ou schizophrénie des fonctions ? Une analyse de Cédric CARTAU DORA et résilience opérationnelle : la gestion des identifiants comme contrôle des risques financiers (en) ISO 27001-NIST CSF- IEC 62443 … Penser qu’un seul référentiel suffit en cybersécurité OT est déjà une approximation. Mais croire qu’ils jouent tous le même rôle en est une autre … un post de Ndeye Adama DRAME sur LinkedIn Planifier la reprise d’activité après un incident : les 11 étapes clés Les réinitialisations régulières de mots de passe ne sont pas aussi sûres qu’on le croit (en) Des pirates obtiennent via Teams un accès distant aux postes de salariés La persévérance plutôt que l’impact : les leçons tirées du front ukrainien de la cyberguerre (en) Et puis, dans la vie personnelle comme dans la vie professionnelle Des fermes de cartes SIM vous inondent de SMS frauduleux – et comment se protéger Arnaque Leboncoin en 2026 : comment un vendeur a perdu 1550 euros Veille de veille(s) Sur LinkedIn, la lettre de veille hebdomadaire de Francis BRUCKMANN, Administrateur de l’ARCSI, concernant la semaine 17 (du 20 au 26 avril) et rapportant les faits marquants en sécurité et technologies de l’Information Cyberhebdo du 24 avril 2026 : mauvaise semaine pour le secteur public, le Cyberhebdo LeMagIT RadioCSIRT : le podcast cybersécurité quotidien de Marc-Frédéric GOMEZ Mimétisme, carte postale et jeux vidéos, la cyber-revue de la semaine de Rayna STAMBOLIYSKA La protection des données personnelles – RGPD / GDPR le règlement européen et plus … Vote par correspondance électronique : la CNIL met à jour sa recommandation Depuis le RGPD, les fuites de données explosent-elles vraiment ? Adieu Microsoft et bonjour Scaleway pour l’hébergement des données de santé des Français (voir aussi la lettre de veille du 23 avril) La Plateforme des données de santé fait le choix du cloud souverain avec Scaleway “Une alternative européenne crédible et compétitive existe”: le gouvernement choisit le Français Scaleway pour remplacer Microsoft et héberger nos données de santé La France retire ses dossiers médicaux à Microsoft pour les confier au groupe Iliad Les problématiques des (r)évolutions numériques en cours Des nouvelles du CyberFront DÉCRYPTAGE. Piratages, fuites de données : pourquoi la France est autant ciblée Comment les attaquants se cachent en utilisant la virtualisation Les agences de cybersécurité signalent l’utilisation de réseaux clandestins par des acteurs liés à la Chine à des fins d’espionnage et d’opérations offensives (en) Défense contre les réseaux clandestins d’appareils compromis liés à la Chine. Changement généralisé des tactiques, techniques et procédures (TTP) des cybermalveillants liés à la Chine, analyse et recommandations du NCSC, le Centre national de cybersécurité britannique (en) Le paysage des cybermenaces en Chine évolue rapidement (en) La Chronologie des cyberattaques du 1er au 15 avril 2026 d’Hackmageddon (en) Le Cambodge pressé par la Chine d’”éradiquer totalement” les centres de cyberfraude TheGentlemen, une enseigne de ransomware aux débuts fracassants Kyber, ce ransomware qui teste le chiffrement post-quantique sur Windows Le gang de ransomware Kyber joue avec le chiffrement post-quantique sur Windows Double menace du ransomware Kyber : explication des attaques contre Windows et ESXi, l’analyse technique de Rapid7 (en) En Russie, Internet est en train de disparaître Royaume-Uni : les données médicales de 500 000 personnes proposées à la vente en Chine Données médicales volées de 500 000 volontaires britanniques mises en vente sur un site chinois Après avoir été téléchargées légalement par trois centres de recherches chinois, les données médicales de 500.000 Britanniques se sont retrouvées en vente sur Alibaba, une enquête est en cours En Allemagne, une cyberattaque “extrêmement préoccupante” de la messagerie Signal touche la classe politique, la Russie suspect numéro un Le jeune hacker “HexDex”, soupçonné d’une vague de cyberattaques, a été mis en examen et écroué (voir aussi la lettre de veille du 23 avril) Un hackeur, surnommé “HexDex”, mis en examen et écroué après plusieurs cyberattaques visant notamment des fédérations sportives “Pour gagner de l’argent, je n’ai pas de limite” : l’édifiant CV d’HexDex, le hackeur mis en examen pour avoir volé les données de millions de Français, accès abonnés LeFigaro Parcoursup victime d’une cyberattaque : les données de 705.000 anciens candidats piratées Catastrophe, cette fois, c’est Parcoursup qui se fait pirater ! 705 000 candidats concernés par une fuite de données Fuite de données chez Parcoursup : la cyberattaque est passée inaperçue pendant cinq mois Parcoursup piraté : les données de 705 000 candidats voléesLa plateforme Parcoursup a été piratée : ce que l’on sait de cette intrusion inédite Incident de sécurité affectant les données de certains candidats des sessions Parcoursup 2023 et 2025 résidant ou ayant formulé des vœux en Occitanie, le communiqué de presse du ministère Les Magasins U ont été piratés : les données des clients ont été compromises Cyberattaque chez les magasins U : pensez à changer votre mot de passe Matière à réflexions La cybersécurité est une “priorité géopolitique”, pas un “problème technique” (1/3), un article de Jean-Marc MANACH, accès abonnés Next Études, enquêtes et référentiels APT, ingénierie sociale et red teaming, ce que les données 2025 de Kaspersky révèlent sur l’exposition réelle des secteurs critiques Séminaires – Conférences – Journées Rejoignez le collectif Cybermois 2026 ! Cybermois 2026. Engageons-nous ensemble pour le Cybermois ! Le message de Cybermalveillance.gouv.fr sur LinkedIn Une première compétition de cybersécurité en Alsace : malgré le retard du Grand Est dans le numérique, “on a des talents ici” Intelligence artificielle, sécurité et plus … IA au service de la sécurité … ou pas Les risques de l’IA agentique autonome vus par l’ANSSI L’hameçonnage par IA est la méthode de prédilection des cybercriminels (en) Les mauvais souvenirs hantent encore les agents IA Google Cloud dévoile sa nouvelle stratégie de cybersécurité face à l’essor de l’IA “Combattre l’IA par l’IA” : Face à l’explosion des menaces, Google Cloud mise sur l’IA agentique pour transformer les métiers de la cybersécurité Comment Claude Desktop installe une porte dérobée dans vos navigateurs sans vous le dire Claude Desktop : Anthropic, champion autoproclamé de l’IA responsable, préinstalle discrètement un accès à vos sessions navigateur, y compris pour des logiciels que vous n’avez pas encore installés, la fin de l’article est réservé aux abonnés De l’Australie à l’Europe, en passant par les États-Unis, comment Anthropic est devenu, avec son tout nouveau modèle frontière, la star du moment de la cybersécurité sur BFM Tech Mythos: l’intelligence artificielle qui fait trembler la finance mondial dans “Aujourd’hui l’économie” sur RFI Cybersécurité : Mythos, l’intelligence artificielle d’Anthropic qui protège… et inquiète Souveraineté numérique et Claude Mythos : Un appel à l’action et nos propositions pour la France, l’Europe et l’open source IA & cybersécurité : un basculement imminent ? … Un post du CLUSIF Un agent IA chinois a trouvé près de 1 000 failles inédites, dont certaines dans Microsoft Office Interrogations / Perspectives / Prospectives IA Secure : sommes-nous vraiment impuissants face à la menace ? Les agents IA vont-ils changer la nature même du travail en entreprise ? C’est la vision de Google avec Workspace Intelligence et Gemini Enterprise Information L’IA au sommaire de l’émission de Frédéric SIMOTTEL sur BFM Tech&Co le 21 avril La note qui annonce une nouvelle phase dans la guerre de l’IA L’IA fait passer les jumeaux numériques dans une autre dimension 10 Bits : La liste critique de l’actualité des données du 18 au 24 avril (en) Enseignement L’intelligence artificielle de pointe, une information du Centre canadien pour la cybersécurité Anthropic offre (discrètement) 13 formations gratuites, un post de Clément PREDO sur LinkedIn Recherche, développement et application Les États-Unis accusent la Chine de voler leur IA “à l’échelle industrielle” via la technique de distillation : Pékin dénonce une “calomnie” et DeepSeek, visé implicitement, publie son modèle V4, la fin de l’article est réservée aux abonnés L’entreprise chinoise DeepSeek lance un nouveau modèle d’intelligence artificielle 7 fois moins cher que Claude Opus 4.7 : la Chine dégaine DeepSeek-V4, un modèle open source conçu pour vous détourner des États-Unis OpenAI dévoile GPT-5.5 et veut faire une remontada historique face à Claude et Gemini OpenAI dévoile GPT-5.5 et veut faire une remontada historique face à Claude et Gemini OpenAI dégaine son nouveau modèle GPT-5.5 et lance un défie à Anthropic GPT-5.5 : les promesses d’OpenAI contredites par les premiers retours Google a une arme secrète pour gagner la guerre de l’IA : les TPU 8t et TPU 8i Entreprises – Économie – Business Une part des bénéfices de l’IA effacée par la correction d’erreurs Cette sélection, parfaitement partielle et partiale, de sujets proposés irrégulièrement à votre attention n’est possible que par le travail de veille et de partage réalisé en amont par différentes sources que je remercie. A votre disposition pour recueillir vos observations, suggestions, commentaires et … demandes de suspension d’envoi, bien évidemment. Avec mes cordiales salutations. Lionel Guillet Une précision – Les recherches ciblées sur les lettres de veille archivées sont désormais possibles par l’intermédiaire d’un widget sur la page d’accueil du site https://veillecyberland.wordpress.com/ Un mot-clé, sa validation, et le système vous affiche la liste des lettres qui le contiennent.Il suffit alors de cliquer sur le lien hypertexte de chacune des lettres pour les ouvrir et lancer une recherche par CTRL+F sur leur contenu. La transaction manque d’élégance, mais elle est efficace. Elle peut vous être utile pour une étude, pour préparer une intervention, une présentation, etc. À votre disposition pour recueillir vos observations, suggestions et commentaires sur cette information guillet.lionel@gmail.com
- Veille Cyber N593 – 27 avril 2026par veillecybertb le 30 avril 2026 à 10h04
Veille hebdomadaire du 26 avril 2026 CyberStratégie /CyberDéfense / CyberSécurité – Protection des données / RGPD – Intelligence artificielle … Lettre Cyber 593 L’actualité cyber du 20 au 26 avril 2026 …… faits, chroniques et opinions, référentiels, séquences audio, séquences vidéo … selon vos centres d’intérêt, personnels ou professionnels, je vous laisse découvrir l’actualité de la semaine, dans ces domaines essentiels que sont … la CyberStratégie, la CyberSécurité, la protection des données personnelles et l’intelligence artificielle … sans prétention à l’exhaustivité et avec beaucoup de subjectivité, inévitable, bien évidemment. Une bonne semaine à vous. Sans oublier que je reste à l’écoute de vos commentaires et de vos observations guillet.lionel@gmail.com Ce qui a retenu mon attention dans l’actualité de cette semaine 21 avril 2026. Toutes les vidéos des auditions de la Commission d’enquête de l’Assemblée nationale sur les dépendances numériques sont en ligne – L’Agence Nationale des Titres Sécurisés … pas tant que cela, nouvelle fuite massive de données à caractère personnel gérées par un service public, l’ANTS touchée par une cyberattaque – Fuite de données chez Vercel, une plateforme de développement cloud. A l’origine, une application d’IA tierce … A(ré)écouter – A (re)voir Cyberattaques : les collectivités territoriales, particulièrement ciblées, doivent apprendre à résister dans la chronique “Nouveau monde” de Nicolas ARPAGIAN sur FranceInfo (voir aussi la lettre de veille du 19 avril) Toutes les vidéos des auditions de la Commission d’enquête de l’Assemblée nationale sur les dépendances structurelles et les vulnérabilités dans le secteur numérique et les risques pour l’indépendance de la France sont ici … Des ministères cherchent des alternatives aux éditeurs logiciels US Le rapport M-Trends 2026 de Mandiant analysé au micro de l’équipe NoLimitSecu cette semaine avec David GROUT Histoire de la Cyber Française – FSSI, Matignon & Santé avec Philippe Loudenot, une vidéo de son interview Informations Négationnisme, deepfakes, usurpation d’identité… On vous résume les accusations qui visent le réseau X et pour lesquelles Elon Musk est convoqué devant la justice française Affaire X : le bras de fer entre Elon Musk et la justice français entre dans sa phase critique La Commission européenne met 180 millions sur le cloud souverain, voici qui sont les gagnants Loi SREN : le décret attendu qui redéfinit les règles du cloud pour les administrations Management de la sécurité de l’Information Cybersécurité : quand la menace oblige à repenser le périmètre de la sécurité Identités sous pression : quand l’IA et la cryptographie redessinent la surface d’attaque Les réseaux sociaux professionnels, terrain de chasse de nombreux services de renseignement, un livret de sensibilisation de la DGSI, la Direction Générale de la Sécurité Intérieure Sécurité économique : Pourquoi la DGSI recommande aux entreprises de bannir certaines solutions SaaS étrangères (voir aussi la lettre de veille du 19 avril sur le flas ingérence de la DGSI) L’ensemble des interviews du Global Security Mag dans le contexte du Forum InCyber qui a eu lieu du 31 mars au 2 avril ici … Cyberassurance : les conflits de 2026 durcissent les clauses de guerre SOC : comment améliorer l’expérience des analystes et pourquoi c’est important Fuite de données ou violation de données ? Votre stockage en cloud est-il compatible avec l’IA ? Cybersécurité OT et IA, 5 stratégies contre les cybermenaces L’identité est le nouveau périmètre : surmonter les points faibles d’Active Directory Comment la réduction des activités de gestion des CVE par le NIST affecte les équipes de cybersécurité (en) (voir aussi la lettre de veille du 19 avril) La fonction Recall dans Windows reste toujours vulnérable Et puis, dans la vie personnelle comme dans la vie professionnelle Quels conseils de cybersécurité pour les Français de l’étranger, en première ligne ? Veille de veille(s) Le bulletin d’actualité du 20 avril du CERT-FR, un retour sur “les vulnérabilités significatives de la semaine passée pour souligner leurs criticités” Vulnérabilités : les 12 alertes critiques du 19 avril 2026. “L’hebdo” cybersécurité de Marc BARBEZAT actualisé tous les jours La Veille cyber hebdomadaire N.592 est en ligne, un retour sur la semaine du 13 au 19 avril 2026, sans oublier son extrait dédié intelligence artificielle RadioCSIRT : le podcast cybersécurité quotidien de Marc-Frédéric GOMEZ La protection des données personnelles – RGPD / GDPR le règlement européen et plus … Revoir le webinaire – Élections municipales 2026 : quelles sont les nouvelles règles de ciblage électoral ? La CNIL vous propose … Le bulletin d’information 119 du Contrôleur européen de la protection des données est en ligne (en) RGPD & messagerie professionnelle : l’arrêt qui change tout … un post de Cyrille CARDONNE sur LinkedIn Des nouvelles du CyberFront Chronologie des fuites de données de 1998 à 2026. ZATAZ relance son musée des sites et entreprises piratés avec une frise pensée comme un outil d’alerte, de mémoire et de lecture immédiate du risque cyber Ransomware : une économie qui change d’échelle Ransomware : derrière certaines cyberattaques, l’ombre de Moscou Sur le dark web, une identité complète vaut à peine 35 dollars Cyber attaque : signalement cyber obligatoire en quatre heures, c’est la réglementation nigérienne qui l’impose Cyberattaque : comment des hackers volent le fret routier américain. Ils piratent des transporteurs et volent des cargaisons entières Le Canada se trouve à un moment charnière de la lutte contre la criminalité financière L’éducation nationale, une cible vulnérable face aux cyberattaques, accès abonnés LeMonde L’Agence nationale des titres sécurisés a été visée par une attaque informatique, des données potentiellement “divulguées”, annonce le ministère de l’Intérieur Fuite de données après un “incident de sécurité” visant le portail de l’Agence nationale des titres sécurisés (ANTS) Piratage ANTS (France Titres) : quelles données personnelles ont fuité ? Cybersécurité : L’Agence nationale des titres sécurisés (ANTS), qui gère la délivrance des cartes d’identité, passeports et permis de conduire, a été victime d’une fuite de données Incident de sécurité à l’ANTS : Ce que les entreprises et les usagers doivent savoir L’ANTS piratée à cause d’une faille basique et 19 millions de Français en font les frais, une fois de plus ! Incident de sécurité relatif au portail ants.gouv.fr, le communiqué de presse du ministère de l’intérieur Communication sur la fuite présumée de données d’état civil, le communiqué de l’ANTS Au Muséum national d’histoire naturelle, 7 000 factures en retard neuf mois après une cyberattaque, accès abonnés LeMonde Matière à réflexions “Cyberconflits” ou pas ? Une réalité diffuse complexe à appréhender Séminaires – Conférences – Journées NIS2, RGPD : éclairages sur deux réglementations phares de la sécurité numérique, une Matinale du CyberCercle Auvergne-Rhône-Alpes le 23 avril à Lyon Intelligence artificielle, sécurité et plus … IA au service de la sécurité … ou pas Le modèle Mythos d’Anthropic déclenche une réorganisation d’urgence de la cybersécurité mondiale Yoshua Bengio sonne l’alarme sur Mythos, l’IA et la menace d’une cybersécurité hors de contrôle Agents IA: les experts en cybersécurité alertent sur des risques croissants AI Index Report 2026 de Stanford : L’IA accélère, mais les garde-fous peinent à suivre (voir aussi la lettre de veille du 19 avril) Les incidents impliquant des agents IA sont désormais monnaie courante selon une étude de la Cloud Security Alliance (en) Les agents d’IA sont à l’origine d’incidents de cybersécurité dans deux tiers des entreprises La NSA utilise en secret Mythos Preview, le modèle le plus puissant d’Anthropic, l’entreprise officiellement bannie par le Pentagone qui est censée représenter un “risque pour la sécurité nationale” (la fin de l’article est réservée aux abonnés) L’Ukraine s’apprête à remplacer ses soldats de première ligne par 25 000 robots terrestres sans pilote, pour faire passer entièrement la logistique de première ligne à des systèmes robotiques Une faille exploitée dans Nginx expose des serveurs MCP Piratage chez Vercel via un outil d’IA : des données potentiellement mises en vente Vercel piraté via un outil IA tiers qui avait les clés du royaume Victime d’une intrusion, Vercel évoque un vol d’identifiants via un outil IA tierce partie Des données de Vercel compromises par une application IA tierce Vercel victime d’une intrusion via une attaque de la chaîne d’approvisionnement par une IA contextuelle (en) Des intrus assistés par l’IA ont pris le contrôle de Vercel via une violation du protocole OAuth et le vol d’un compte d’employé (en) Interrogations / Perspectives / Prospectives “C’est comme donner les plans d’une chambre forte” : pourquoi l’IA a poussé cette entreprise à abandonner l’open source En automatisant les tâches, l’IA menace plusieurs métiers (voir aussi les lettres de veille du 24 mars et du 2 avril) Pour OpenAI, 18 % des métiers présentent “un risque élevé d’automatisation à court terme” Un cadre de transition pour les emplois dans le domaine de l’IA. Cartographie de l’impact à court terme de l’IA sur l’emploi, l’étude d’OpenAI [pdf] Plus de peur que de mal… IA et automatisation ne signifieraient pas forcément “perte d’emploi” humain ! Un post de Françoise HALPER sur LinkedIn Intelligence artificielle : plus d’un emploi sur deux transformé d’ici trois ans (en) Plus on délègue à l’IA, moins on sait faire sans elle : le paradoxe de l’augmentation cognitive qui finit par amputer la cognition qu’elle prétendait amplifier, selon des études (la fin de l’article est réservée aux abonnés) Information Panne ChatGPT, Gemini et Claude : pourquoi les IA ne fonctionnent plus ? La demande en compétence agentique bondit de 60% en France 10 Bits : La liste critique de l’actualité des données du 4 au 10 avril (en) 10 Bits : La liste critique de l’actualité des données du 11 au 17 avril (en) Santé ZD Tech : Raisonnement mirage, pourquoi GPT-5 et Gemini 3 Pro inventent des diagnostics médicaux, à écouter dans le podcast “3 minutes pour comprendre” Recherche, développement et application IA agentique : comment guider l’avènement des citizen developers Avec Claude Design, Anthropic veut tuer PowerPoint, InDesign et Figma Claude Design : Le nouveau séisme d’Anthropic qui fait trembler les géants du design Entreprises – Économie – Business Les services, nouvel eldorado de l’IA La moitié des salariés américains utilisent désormais l’IA au travail – et y consacrent près de 8 heures par semaine 23 avril 2026. Cycle de vie du développement, de l’intégration et du déploiement logiciel … l’ANSSI publie une étude du marché européen – Enfin, ça y est ! Les données de santé des français ne seront plus hébergées par Microsoft. La plateforme Health Data Hub change d’hébergeur pour l’entreprise française Scaleway – Des acteurs publics (ministères, police …) des infrastructures sportives et culturelles, des entreprises du secteur privé …, l’auteur de multiples cyberattaques récentes a été arrêté. A noter que la fuite de données de l’ANTS ; l’Agence nationale des titres (mal) sécurisés, ce n’est pas lui. – A l’origine de la fuite de données de l’ANTS, peut-être bien un défaut de configuration messagerie … A(ré)écouter – A (re)voir Cybersécurité et réglementation, frères ennemis ou alliés ? Une table ronde RiskIntel Media animée par Yasmine DOUDO Les attaquants ne piratent plus, ils se connectent : l’explosion des secrets exposés, dans le podcast “InCyber” Informations Lien armées-nation : le Commandement de la cyberdéfense rencontre les étudiants de la Sorbonne La DGSI met en garde les entreprises contre les applications et logiciels étrangers (voir aussi la lettre de veille du 21 avril) Management de la sécurité de l’Information IA et cybersécurité : anticiper aujourd’hui pour maîtriser demain, présentation de la note du Conseil de l’IA et du numérique publiée ce jour IA et cybersécurité : anticiper aujourd’hui pour maîtriser demain [pdf] Cybersécurité : face aux bouleversements de l’IA, un appel à “ne pas céder à la panique”, accès abonnés LeMonde Dossier : 2026, l’année de tous les risques, un dossier LeMondeInformatique Après le chiffrement du trafic, la prochaine bataille se jouera-t-elle sur la vérification anonyme ? RSSI : 7 red flag qui doivent vous faire refuser un poste, un article JDN accessible gratuitement sous réserve d’inscription La cybersécurité est avant tout une affaire de gouvernance Cybersécurité : tout ce que les attaquants savent déjà sur votre entreprise S-SDLC et DevSecOps en Europe : Enjeux actuels et perspectives d’avenir. La sécurisation du cycle de développement logiciel n’est plus une option : c’est un enjeu stratégique ! Une nouvelle publication de l’ANSSI Étude de marché : S-SDLC / DEVSECOPS. Quels sont les défis actuels et futurs du marché européen ? La sécurisation du cycle de développement logiciel est un enjeu stratégique … un post de l’Agence sur LinkedIn DevSecOps européen : bien outillé, mais encore dominé Le mythe de la sauvegarde qui met les entreprises en danger (en) Et puis, dans la vie personnelle comme dans la vie professionnelle Fuite de données à l’ANTS : Pourquoi faut-il particulièrement se méfier en mai des cyberattaques ? Cyberattaque de l’ANTS : que faire si je suis victime d’une usurpation d’identité ? Cyberattaque massive de l’ANTS : ce qu’il faut savoir si vous êtes concernés (voir également la rubrique “Des nouvelles du CyberFront”) Veille de veille(s) La newsletter hebdomadaire Threat Landscape Intrinsec du 23 avril 2026 La protection des données personnelles – RGPD / GDPR le règlement européen et plus … Health Data Hub : Scaleway succède à Microsoft pour bâtir le sanctuaire des données de santé françaises Données de santé : le Health Data Hub quitte Microsoft Azure pour Scaleway Scaleway remporte l’hébergement des données de santé à la place de Microsoft Lignes directrices pour la recherche scientifique et certification : les derniers documents adoptés par le CEPD, le Comité européen de la protection des données Les problématiques des (r)évolutions numériques en cours Souveraineté numérique : l’Europe peut-elle s’affranchir des États-Unis ? L’automatisation alimente l’IA : le moteur caché derrière des analyses intelligentes Des nouvelles du CyberFront La guerre dans le champ électromagnétique : un enjeu stratégique invisible mais déterminant, le communiqué de presse du ComCyber, le Commandement de la cyberdéfense Des frissons et un tremplin : comment l’armée de Terre séduit la Gen Z de la cybersécurité Ce malware Android retourne votre reconnaissance faciale contre vous pour vider vos comptes bancaires Des données patients dérobées aux espaces numériques régionaux de santé en 2025 ressurgissent sur le “dark web”, un article accessible gratuitement sur simple inscription sur le site TICSanté Cyberattaque en Iran : pourquoi les routeurs américains tombent en panne sans internet. Des équipements réseau iraniens tombent en panne malgré le blackout internet : voici les quatre hypothèses de Téhéran Des médias iraniens allèguent que les USA ont fait usage de portes dérobées dans des équipements réseau de fabrication américaine pour entraver les frappes militaires de l’Iran lors de moments critiques Londres. Métro : 10 millions de profils exposés après le piratage Un négociateur de rançongiciels plaide coupable dans l’affaire BlackCat (en) Un hackeur interpellé en Vendée après plusieurs cyberattaques visant notamment des fédérations sportives Angel Batista et Hexdex, le piège se referme ? HexDex interpellé, enquête ouverte en France Cyberattaques : le hacker surnommé “HexDex” est placé en garde à vue Arrestation de HexDex, pirate français spécialiste du vol de bases de données, l’analyse de Valéry RIEß-MARCHIVE Permis, CNI, passeports : vol de données après la cyberattaque de l’ANTS (voir aussi la lettre de veille du 21 avril) Incident de sécurité relatif au portail ants.gouv.fr : point d’étape du 21 avril 2026, le communiqué de presse du ministère de l’intérieur La fuite de données à l’ANTS, nouvelle illustration des failles de sécurité des services informatiques de l’État, accès abonnés LeMonde Fuite de données sur le portail de l’ANTS : près de 12 millions de comptes concernés, annonce le ministère de l’Intérieur La fuite ANTS, un leak bidon ? Derrière l’annonce d’un vol massif de données ANTS : Le “pirate” Breach3d s’explique … L’ANTS vient d’être piratée : entre 11 et 19 millions de Français concernés. Le hacker lui-même a qualifiée la faille utilisée de “vraiment stupide” … un post de Samuel KOHEN sur LinkedIn Pourquoi le piratage de France Titres (ANTS) aurait pu être évité d’après un spécialiste L’ANTS confirme un incident cyber : une configuration DMARC inactive depuis au moins 2019 Modifier un chiffre dans une URL pour accéder aux données de 19 millions de Français : le portail de l’ANTS cède face à une vulnérabilité basique, votre nom, prénom, date de naissance sont peut-être en vente Une faille sur France Titres (ANTS) expose des logs serveur et dumps mémoire accessibles en ligne, une nouvelle faille potentielle signalée par FrenchBreaches Matière à réflexions Fuite ANTS : l’État doit nous protéger et non nous exposer, une chronique de Yasmine DOUADIs Analyse coûts-avantages-risques de la R&D en cybersécurité, une étude parue dans le Journal de la cybersécurité d’Oxford University Press (en) Au Moyen-Orient, la guerre se joue aussi sur les écrans : “L’enjeu premier et final, c’est le contrôle du récit”, une interview du commandant Samuel HENRY, spécialiste de la guerre informationnelle Études, enquêtes et référentiels Évaluez vos capacités et votre maturité en matière de cybersécurité nationale à l’aide du cadre ENISA mis à jour (en) L’ENISA met à jour le NCAF 2.0 pour aider les gouvernements à mesurer et combler les lacunes en matière de cybersécurité, et à promouvoir l’évaluation comparative de la maturité en cybersécurité (en) Intelligence artificielle, sécurité et plus … IA au service de la sécurité … ou pas Le gouvernement britannique alerte sur les risques cyber des nouveaux modèles d’IA Cybersécurité : Londres alerte sur les risques liés aux nouveaux modèles d’IA Conserver un avantage défensif à l’ère des cyber-capacités d’IA de pointe (en) Intelligence artificielle : “zero day” after Sans une cybergouvernance solide, ce potentiel peut rapidement se transformer en risque Agent Skills et IA autonome, le nouveau défi cybersécurité Mythos, IA et cybersécurité : la fin du mythe de l’exclusivité La plupart des entreprises sont incapables de contrer les menaces posées par les agents d’IA de niveau 3, selon une enquête de VentureBeat (en) IA et automatisation : gains opérationnels et zones de vigilance La plupart des “SOC IA” se contentent d’un triage plus rapide. Ce n’est pas suffisant (en) Ils traquent les modèles d’IA cachés, tombent sur Claude Mythos et n’en font pratiquement rien. En tout cas, c’est ce qu’ils disent Fuite Claude Mythos : comment des utilisateurs ont accédé à l’IA d’Anthropic Anthropic enquête après un accès non autorisé à son modèle d’IA Mythos “Les jours des zero-days sont comptés” : Claude Mythos a donné des sueurs froides à Firefox, et ça a payé Les zero-days sont comptés. Firefox 150 intègre des correctifs pour 271 vulnérabilités découvertes par Claude Mythos Preview . Le communiqué de presse (en) L’IA peut-elle attaquer le cloud ? Leçons tirées de la construction d’un système multi-agents offensif autonome dans le cloud, une étude Unit42 Interrogations / Perspectives / Prospectives Cyber : Google investit 32 milliards de dollars dans une cyberarmée d’agents IA Une start-up veut confier la vérité à un “tribunal IA” chargé de juger les journalistes dans “Bientôt chez vous” sur France Info Information Meta transforme l’activité de ses salariés en “carburant” pour ses agents IA IA & Cybersécurité : les 11 actus clés du 22 avril 2026 de Marc BARBEZAT Recherche, développement et application Avec ChatGPT Images 2.0, OpenAI déclare la guerre à Google et veut vous faire oublier Nano Banana Entreprises – Économie – Business IA agentique : les nouvelles compétences que les entreprises recherchent (à rapprocher de La demande en compétence agentique bondit de 60% en France) Ces entreprises forment leurs employés à l’IA : voici comment elles s’y prennent Le développement à grande échelle de l’IA agentique nécessite des données solides : 4 étapes à suivre en premier lieu IA : cinq signaux d’alerte révélateurs des limites d’une infrastructure 26 avril 2026. Les données médicales de 500 000 patients britanniques mises en vente sur Alibaba avant d’être promptement enlevées – Se défendre contre les réseaux clandestins d’appareils compromis liés à la Chine, une alerte des agences internationales de cybersécurité – Cette fois, c’est Parcoursup qui a été touché, plus exactement 705 000 candidats des sessions 2023 et 2025 inscrits en Occitanie. Noms, prénoms, nationalité, date de naissance, adresses, téléphones dérobés… l’ordinaire, quoi ! Les magasins U aussi avec le N . de carte de fidélité en plus … A(ré)écouter – A (re)voir Sommes-nous encore en sécurité sur le net ? Vidéo d’un “Cyber talk” RiskIntel avec Eric ANTIBI Informations Affaire du porte-avions Charles-de-Gaulle : le chef d’Etat-major calme le jeu La Dinum précise sa feuille de route de bascule sur Linux Passage de Windows à Linux : pourquoi la France s’apprête à tourner le dos aux outils numériques américains Management de la sécurité de l’Information RSSI et DPO : complémentarité ou schizophrénie des fonctions ? Une analyse de Cédric CARTAU DORA et résilience opérationnelle : la gestion des identifiants comme contrôle des risques financiers (en) ISO 27001-NIST CSF- IEC 62443 … Penser qu’un seul référentiel suffit en cybersécurité OT est déjà une approximation. Mais croire qu’ils jouent tous le même rôle en est une autre … un post de Ndeye Adama DRAME sur LinkedIn Planifier la reprise d’activité après un incident : les 11 étapes clés Les réinitialisations régulières de mots de passe ne sont pas aussi sûres qu’on le croit (en) Des pirates obtiennent via Teams un accès distant aux postes de salariés La persévérance plutôt que l’impact : les leçons tirées du front ukrainien de la cyberguerre (en) Et puis, dans la vie personnelle comme dans la vie professionnelle Des fermes de cartes SIM vous inondent de SMS frauduleux – et comment se protéger Arnaque Leboncoin en 2026 : comment un vendeur a perdu 1550 euros Veille de veille(s) Sur LinkedIn, la lettre de veille hebdomadaire de Francis BRUCKMANN, Administrateur de l’ARCSI, concernant la semaine 17 (du 20 au 26 avril) et rapportant les faits marquants en sécurité et technologies de l’Information Cyberhebdo du 24 avril 2026 : mauvaise semaine pour le secteur public, le Cyberhebdo LeMagIT RadioCSIRT : le podcast cybersécurité quotidien de Marc-Frédéric GOMEZ Mimétisme, carte postale et jeux vidéos, la cyber-revue de la semaine de Rayna STAMBOLIYSKA La protection des données personnelles – RGPD / GDPR le règlement européen et plus … Vote par correspondance électronique : la CNIL met à jour sa recommandation Depuis le RGPD, les fuites de données explosent-elles vraiment ? Adieu Microsoft et bonjour Scaleway pour l’hébergement des données de santé des Français (voir aussi la lettre de veille du 23 avril) La Plateforme des données de santé fait le choix du cloud souverain avec Scaleway “Une alternative européenne crédible et compétitive existe”: le gouvernement choisit le Français Scaleway pour remplacer Microsoft et héberger nos données de santé La France retire ses dossiers médicaux à Microsoft pour les confier au groupe Iliad Les problématiques des (r)évolutions numériques en cours Des nouvelles du CyberFront DÉCRYPTAGE. Piratages, fuites de données : pourquoi la France est autant ciblée Comment les attaquants se cachent en utilisant la virtualisation Les agences de cybersécurité signalent l’utilisation de réseaux clandestins par des acteurs liés à la Chine à des fins d’espionnage et d’opérations offensives (en) Défense contre les réseaux clandestins d’appareils compromis liés à la Chine. Changement généralisé des tactiques, techniques et procédures (TTP) des cybermalveillants liés à la Chine, analyse et recommandations du NCSC, le Centre national de cybersécurité britannique (en) Le paysage des cybermenaces en Chine évolue rapidement (en) La Chronologie des cyberattaques du 1er au 15 avril 2026 d’Hackmageddon (en) Le Cambodge pressé par la Chine d’”éradiquer totalement” les centres de cyberfraude TheGentlemen, une enseigne de ransomware aux débuts fracassants Kyber, ce ransomware qui teste le chiffrement post-quantique sur Windows Le gang de ransomware Kyber joue avec le chiffrement post-quantique sur Windows Double menace du ransomware Kyber : explication des attaques contre Windows et ESXi, l’analyse technique de Rapid7 (en) En Russie, Internet est en train de disparaître Royaume-Uni : les données médicales de 500 000 personnes proposées à la vente en Chine Données médicales volées de 500 000 volontaires britanniques mises en vente sur un site chinois Après avoir été téléchargées légalement par trois centres de recherches chinois, les données médicales de 500.000 Britanniques se sont retrouvées en vente sur Alibaba, une enquête est en cours En Allemagne, une cyberattaque “extrêmement préoccupante” de la messagerie Signal touche la classe politique, la Russie suspect numéro un Le jeune hacker “HexDex”, soupçonné d’une vague de cyberattaques, a été mis en examen et écroué (voir aussi la lettre de veille du 23 avril) Un hackeur, surnommé “HexDex”, mis en examen et écroué après plusieurs cyberattaques visant notamment des fédérations sportives “Pour gagner de l’argent, je n’ai pas de limite” : l’édifiant CV d’HexDex, le hackeur mis en examen pour avoir volé les données de millions de Français, accès abonnés LeFigaro Parcoursup victime d’une cyberattaque : les données de 705.000 anciens candidats piratées Catastrophe, cette fois, c’est Parcoursup qui se fait pirater ! 705 000 candidats concernés par une fuite de données Fuite de données chez Parcoursup : la cyberattaque est passée inaperçue pendant cinq mois Parcoursup piraté : les données de 705 000 candidats voléesLa plateforme Parcoursup a été piratée : ce que l’on sait de cette intrusion inédite Incident de sécurité affectant les données de certains candidats des sessions Parcoursup 2023 et 2025 résidant ou ayant formulé des vœux en Occitanie, le communiqué de presse du ministère Les Magasins U ont été piratés : les données des clients ont été compromises Cyberattaque chez les magasins U : pensez à changer votre mot de passe Matière à réflexions La cybersécurité est une “priorité géopolitique”, pas un “problème technique” (1/3), un article de Jean-Marc MANACH, accès abonnés Next Études, enquêtes et référentiels APT, ingénierie sociale et red teaming, ce que les données 2025 de Kaspersky révèlent sur l’exposition réelle des secteurs critiques Séminaires – Conférences – Journées Rejoignez le collectif Cybermois 2026 ! Cybermois 2026. Engageons-nous ensemble pour le Cybermois ! Le message de Cybermalveillance.gouv.fr sur LinkedIn Une première compétition de cybersécurité en Alsace : malgré le retard du Grand Est dans le numérique, “on a des talents ici” Intelligence artificielle, sécurité et plus … IA au service de la sécurité … ou pas Les risques de l’IA agentique autonome vus par l’ANSSI L’hameçonnage par IA est la méthode de prédilection des cybercriminels (en) Les mauvais souvenirs hantent encore les agents IA Google Cloud dévoile sa nouvelle stratégie de cybersécurité face à l’essor de l’IA “Combattre l’IA par l’IA” : Face à l’explosion des menaces, Google Cloud mise sur l’IA agentique pour transformer les métiers de la cybersécurité Comment Claude Desktop installe une porte dérobée dans vos navigateurs sans vous le dire Claude Desktop : Anthropic, champion autoproclamé de l’IA responsable, préinstalle discrètement un accès à vos sessions navigateur, y compris pour des logiciels que vous n’avez pas encore installés, la fin de l’article est réservé aux abonnés De l’Australie à l’Europe, en passant par les États-Unis, comment Anthropic est devenu, avec son tout nouveau modèle frontière, la star du moment de la cybersécurité sur BFM Tech Mythos: l’intelligence artificielle qui fait trembler la finance mondial dans “Aujourd’hui l’économie” sur RFI Cybersécurité : Mythos, l’intelligence artificielle d’Anthropic qui protège… et inquiète Souveraineté numérique et Claude Mythos : Un appel à l’action et nos propositions pour la France, l’Europe et l’open source IA & cybersécurité : un basculement imminent ? … Un post du CLUSIF Un agent IA chinois a trouvé près de 1 000 failles inédites, dont certaines dans Microsoft Office Interrogations / Perspectives / Prospectives IA Secure : sommes-nous vraiment impuissants face à la menace ? Les agents IA vont-ils changer la nature même du travail en entreprise ? C’est la vision de Google avec Workspace Intelligence et Gemini Enterprise Information L’IA au sommaire de l’émission de Frédéric SIMOTTEL sur BFM Tech&Co le 21 avril La note qui annonce une nouvelle phase dans la guerre de l’IA L’IA fait passer les jumeaux numériques dans une autre dimension 10 Bits : La liste critique de l’actualité des données du 18 au 24 avril (en) Enseignement L’intelligence artificielle de pointe, une information du Centre canadien pour la cybersécurité Anthropic offre (discrètement) 13 formations gratuites, un post de Clément PREDO sur LinkedIn Recherche, développement et application Les États-Unis accusent la Chine de voler leur IA “à l’échelle industrielle” via la technique de distillation : Pékin dénonce une “calomnie” et DeepSeek, visé implicitement, publie son modèle V4, la fin de l’article est réservée aux abonnés L’entreprise chinoise DeepSeek lance un nouveau modèle d’intelligence artificielle 7 fois moins cher que Claude Opus 4.7 : la Chine dégaine DeepSeek-V4, un modèle open source conçu pour vous détourner des États-Unis OpenAI dévoile GPT-5.5 et veut faire une remontada historique face à Claude et Gemini OpenAI dévoile GPT-5.5 et veut faire une remontada historique face à Claude et Gemini OpenAI dégaine son nouveau modèle GPT-5.5 et lance un défie à Anthropic GPT-5.5 : les promesses d’OpenAI contredites par les premiers retours Google a une arme secrète pour gagner la guerre de l’IA : les TPU 8t et TPU 8i Entreprises – Économie – Business Une part des bénéfices de l’IA effacée par la correction d’erreurs Cette sélection, parfaitement partielle et partiale, de sujets proposés irrégulièrement à votre attention n’est possible que par le travail de veille et de partage réalisé en amont par différentes sources que je remercie. A votre disposition pour recueillir vos observations, suggestions, commentaires et … demandes de suspension d’envoi, bien évidemment. Avec mes cordiales salutations. Lionel Guillet Une précision – Les recherches ciblées sur les lettres de veille archivées sont désormais possibles par l’intermédiaire d’un widget sur la page d’accueil du site https://veillecyberland.wordpress.com/ Un mot-clé, sa validation, et le système vous affiche la liste des lettres qui le contiennent.Il suffit alors de cliquer sur le lien hypertexte de chacune des lettres pour les ouvrir et lancer une recherche par CTRL+F sur leur contenu. La transaction manque d’élégance, mais elle est efficace. Elle peut vous être utile pour une étude, pour préparer une intervention, une présentation, etc. À votre disposition pour recueillir vos observations, suggestions et commentaires sur cette information guillet.lionel@gmail.com
- Rapport annuel 2025 de fedpol : la police accélère sa mutation numériquepar Marc Barbezat le 30 avril 2026 à 8h36
Le rapport annuel 2025 de fedpol détaille la lutte contre le crime organisé et les préparatifs de l'e-ID. Ce document fixe le cap pour la sécurité suisse.
- CVE-2026-42208: LiteLLM bug exploited 36 hours after its disclosurepar Pierluigi Paganini le 29 avril 2026 à 21h02
Attackers quickly exploited a critical LiteLLM flaw (CVE-2026-42208) to access and modify sensitive database data via SQL injection. Attackers rapidly exploited a critical vulnerability in LiteLLM Python package, tracked as CVE-2026-42208, just days after it became public. The vulnerability, an SQL injection in the proxy API key verification process, lets attackers access and potentially modify database data. Instead of safely passing the key as a parameter, it directly inserts the user-supplied value into a database query. This unsafe practice opens the door to SQL injection. An attacker doesn’t need valid credentials. By sending a specially crafted Authorization header to an API endpoint (such as /chat/completions), they can manipulate the query executed by the database. Because the request flows through an error-handling path, the malicious input still reaches the vulnerable query. “A database query used during proxy API key checks mixed the caller-supplied key value into the query text instead of passing it as a separate parameter. An unauthenticated attacker could send a specially crafted Authorization header to any LLM API route (for example POST /chat/completions) and reach this query through the proxy’s error-handling path.” reads the BerriAI’s advisory. “An attacker could read data from the proxy’s database and may be able to modify it, leading to unauthorised access to the proxy and the credentials it manages.” Researchers observed real-world attacks targeting sensitive information stored in database tables, highlighting how quickly disclosed flaws can turn into active threats. The flaw affects LiteLLM versions 1.81.16 to 1.83.6 and was fixed in 1.83.7 on April 19, 2026. The Sysdig Threat Research Team reported that attackers began exploiting it about 36 hours after disclosure. “The Sysdig Threat Research Team (TRT) observed the first exploitation attempt 36 hours and seven minutes after the advisory was published to the global database.” reads the report published by Sysdig. “The traffic the Sysdig TRT captured was not a generic SQLmap spray, which is very common in SQL injection attacks, but a deliberate, and likely customized, enumeration of the production LiteLLM schema, targeting the three tables that hold the highest-value secrets: virtual API keys, stored provider credentials, and the proxy’s environment-variable configuration. The attacker showed strong knowledge of LiteLLM’s database structure and quickly mapped table schemas, but researchers saw no signs of data theft or further compromise. “We did not see follow-through, however. There were no authenticated calls using exfiltrated keys, no virtual-key minting via /key/generate, and no chained reuse of provider credentials.” continues the report. “The novelty of this finding is the speed and precision of the schema-enumeration attempt, not a confirmed compromise.” Sysdig published indicators of compromise for attacks exploiting this vulnerability. Users who can’t upgrade their installs are suggested to enable disable_error_logs: true in general settings to block the attack path and reduce exposure. Follow me on Twitter: @securityaffairs and Facebook and Mastodon Pierluigi Paganini (SecurityAffairs – hacking, LiteLLM)
- Microsoft won’t patch PhantomRPC: Feature or bug?le 29 avril 2026 à 13h34
A researcher has discovered a weakness called PhantomRPC that Microsoft does not consider a vulnerability it plans to patch. PhantomRPC involves Windows Remote Procedure Call (RPC), the core of communication between Windows processes. The vulnerability lets a process with impersonation rights escalate to SYSTEM by impersonating high‑privileged clients that connect to a fake RPC server. The researcher presented a detailed technical report outlining five exploitation paths, including coercion, user interaction, or background services. They warned that potential vectors are “effectively unlimited” because the root issue is architectural. Microsoft, however, classified the issue as “moderate,” refused a bounty, declined to assign a CVE (a spot in the list of Common Vulnerabilities and Exposures), and closed the case without tracking. Its position is that the technique requires an already‑compromised machine and does not provide unauthenticated or remote access. Experts disagreed with Microsoft’s assessment. Their concern is that Microsoft is downplaying a systemic local privilege escalation technique that exists in all supported Windows versions. The issue At the core of this issue is that the Windows RPC runtime does not sufficiently verify that the server a high‑privileged client connects to is the intended legitimate endpoint. If a legitimate RPC server is not reachable (for example because the service stopped, was misconfigured, not installed, or due to a race condition), an attacker with SeImpersonatePrivilege can spin up a fake RPC server that “fills the gap” using the same interface and endpoint. When a SYSTEM or high‑privileged client connects to this fake server, using an impersonation level that allows the server to impersonate the client, the attacker can call RpcImpersonateClient and immediately escalate their privileges to SYSTEM. From Microsoft’s perspective, the ability to run a rogue RPC server in this way falls under the category of “already compromised.” SeImpersonatePrivilege To understand the issue better, we need to dig into what SeImpersonatePrivilege does. Basically, SeImpersonatePrivilege is the Windows permission that lets a program “pretend to be you” after you’ve already logged in, so it can do things on your behalf using your level of access. It’s needed because many system services and server‑type apps (file sharing, RPC servers, COM servers, web apps) have to perform actions on behalf of a user, like reading their files or applying group policy. If an attacker gains this privilege, they can create a fake service or server and wait for a more powerful account to talk to it. When that high‑privilege service connects, the attacker can grab its security token and impersonate it, effectively upgrading from an account with lower privileges to full SYSTEM control on that machine. Protection A Microsoft spokesperson provided the following statement: “This technique requires an already-compromised machine and does not grant unauthenticated or remote access. Any update is a balance between existing compatibility and customer risk, and we remain committed to continually hardening our products. We recommend customers follow security best practices, including limiting administrative privileges and applying the principle of least privilege.” In our opinion, mitigating PhantomRPC properly would require deep changes to the RPC architecture, which is hard to do on existing Windows versions without breaking compatibility. It’s maybe something we’ll see in future versions, given the scale of change needed. What you can do: As PhantomRPC is a piece in a larger chain, it is still very important to keep Windows updated. Use your admin account sparingly and only for the tasks that need that kind of privilege. Use an up-to-date, real-time anti-malware solution that can detect and block suspicious privilege‑escalation activity. Avoid disabling or “hardening” services blindly since a malicious service might step in their place. To answer the question in the title: it looks like a “feature” that can be abused in many ways; one that has outlived its original threat model. Defenders have to treat them as ongoing risks, rather than one‑off CVEs. “One of the best cybersecurity suites on the planet.” According to CNET. Read their review →
- Talkie-1930 - Le LLM qui pense qu'on est en 1930par Korben ✨ le 29 avril 2026 à 9h46
Une IA qui pense que 2026 ressemble à un monde fait de bateaux à vapeur et de vastes réseaux ferroviaires, et qui considère qu'une seconde guerre mondiale est très peu probable... voilà Talkie-1930, le nouveau modèle de langage à 13 milliards de paramètres lancé par Nick Levine, David Duvenaud et Alec Radford (l'un des architectes de GPT-2 chez OpenAI). LE truc avec ce modèle d'un nouveau genre, c'est qu'il n'a JAMAIS lu un mot écrit après le 31 décembre 1930. Pas de Wikipedia, pas de Reddit, pas de GitHub....et j'en passe. Si ça vous branche, vous pouvez tester la démo direct sur talkie-lm.com/chat , et les poids sont dispos sur HuggingFace sous licence Apache 2.0 ! Alors pourquoi 1930 et pas 1950 ou 1900 ? Hé bien tout simplement parce que c'est la date précise à laquelle les œuvres tombent dans le domaine public aux États-Unis. L'équipe a donc pu aspirer 260 milliards de tokens de livres, journaux, périodiques, revues scientifiques, brevets et jurisprudence antérieurs à cette date sans risquer la moindre poursuite légale. Et c'est là que ça devient amusant parce que quand on demande à Talkie-1930 de décrire le futur, il imagine comme je vous le disais en intro, un monde dominé par les bateaux à vapeur et les trains et c'est logique car c'était l'horizon technologique de son corpus à l'époque. Le modèle considère aussi qu'une seconde guerre mondiale est improbable (il ne connaît évidemment que la Première) et du coup, ça donne un terrain d'expérimentation fascinant pour étudier le raisonnement temporel et la généralisation hors distribution moderne. L'équipe a publié trois checkpoints : talkie-1930-13b-base (modèle brut), talkie-1930-13b-it (pour le chat) et talkie-web-13b-base (un jumeau d'architecture identique mais entraîné sur FineWeb à titre de comparaison). Cette approche "modèle jumeau" permet par exemple de mesurer précisément ce qui vient de l'architecture vs ce qui vient des données. Pour la phase de post-training, l'équipe a utilisé Claude Sonnet 4.6 comme juge dans une procédure DPO (Direct Preference Optimization). Ils ont également généré des conversations synthétiques entre Claude Opus 4.6 et Talkie pour le fine-tuning supervisé. Bref, c'est un modèle ultra-vintage entraîné à l'aide de modèles ultra-modernes. L'équipe travaille déjà sur un système OCR custom pour les documents historiques (les OCR conventionnels n'atteignent que 30% de l'efficacité d'apprentissage face à du texte transcrit manuellement) et vise un modèle de niveau GPT-3 pour l'été 2026, avec un corpus pouvant atteindre plus d'un trillion de tokens. Bref, Talkie-1930 c'est un projet de recherche assez chouette pour tous ceux qui aiment creuser les LLMs. Le code est sur GitHub sous Apache 2.0, et la démo en ligne marche très bien si vous voulez juste tester sans installer. Amusez-vous bien ! Source
- The Supreme activates the RGPD from when data are requested, although they are never delivered - apd.catle 29 avril 2026 à 9h32
The Supreme activates the RGPD from when data are requested, although they are never delivered apd.cat
- IA dans la santé : et si le vrai défi était l’organisation des soinspar Sylvia R. le 29 avril 2026 à 8h45
« Le vrai sujet, ce n’est donc pas d’ajouter de l’IA dans la santé. C’est d’utiliser l’IA pour enfin mieux organiser la santé ». Le système de santé français repose encore sur un modèle centré sur l’acte. Le patient consulte quand le symptôme apparaît et sort ensuite du radar. Entre ces moments, un vide persiste. Ni information, ni orientation, ni suivi. Ce vide coûte cher en santé publique. Et c’est exactement ce vide que la donnée permet de combler, réplique Jordan Cohen, le cofondateur et CEO de Tessan. L’entreprise passe d’une solution de téléconsultation à une infrastructure de santé continue. Elle place la donnée et l’IA au centre. Ces dernières relient les moments isolés et structurent le parcours patient. Décryptage. Le vide entre les consultations Depuis longtemps, la santé se limite à la consultation. Elle commence avant et continue après. « Entre les deux, il y a un vide. Un vide d’information, d’orientation et de suivi ». Les patients entrent sans cadre clair puis en sortent sans suivi. Pourtant, les données comblent exactement ce vide, en reliant les moments qui restaient isolés. On ne raisonne plus en actes isolés mais en parcours. Cela change les pratiques, permet de détecter plus tôt et de facto, d’orienter plus vite. Et surtout, on suit dans le temps. Ici, l’IA ne s’ajoute pas comme une couche technologique mais structure la donnée. L’algorithme la qualifie, l’active au bon moment. Chez Tessan qui réalise plus de 3500 téléconsultations par jour, par exemple, la machine intervient à plusieurs niveaux du parcours. En amont, elle organise les symptômes et préremplit les informations utiles. Chez les médecins, elle assure la transcription automatique et aide à la prescription. Chez les partenaires, elle propose des assistants opérationnels. « La vraie rupture, elle est donc là : passer d’une logique d’acte ponctuel à une logique de continuité. Et demain, la valeur en santé ne viendra pas seulement de l’acte médical. Elle viendra de la capacité à organiser la continuité autour du patient », affirme Jordan Cohen. De médecine réactive à une approche proactive Longtemps, le système de santé s’est construit sur une logique réactive. On consulte lorsque les symptômes apparaissent, parfois tardivement, quand la situation s’est déjà dégradée. Cette approche montre aujourd’hui ses limites. L’essor de l’IA en santé ouvre la voie à un changement de paradigme : passer d’une médecine de réaction à une médecine d’anticipation, pilotée par la donnée. Concrètement, l’intégration de l’IA dans la santé permet de capter des signaux en continu. Des bornes de check-up en pharmacie ou des objets connectés du quotidien permettent aussi de relever en temps réel des données essentielles comme la tension artérielle, la fréquence cardiaque ou la saturation en oxygène. Cette masse de données devient alors exploitable grâce à des algorithmes d’IA capables d’identifier des signaux faibles, de détecter des anomalies et de prioriser les actions. Une variation inhabituelle peut ainsi déclencher une alerte et initier rapidement une prise en charge : téléconsultation, téléexpertise ou suivi renforcé. Dans ce modèle, le patient reste en permanence dans le parcours de soins. Il est suivi, relancé et réévalué si nécessaire. « On ne cherche pas à faire du diagnostic automatique. L’objectif, c’est d’améliorer la qualité du signal en amont », note Jordan Cohen. Dans les check-up, l’IA structure symptômes, antécédents et constantes vitales. Elle fait émerger des profils à risque plus tôt. En dermatologie, des modèles internes qualifient les images. Ils priorisent les cas pertinents. D’autres travaux explorent l’estimation de paramètres via vidéo. Ils captent des signaux que le système ignore aujourd’hui. Ces outils aident l’entrée dans le parcours et accélèrent l’orientation sans remplacer le médecin. Les pharmacies, nouveaux hubs de détection et d’accompagnement des patients L’accès aux soins ne suffit plus à elle seule à garantir une prise en charge efficace. L’enjeu devient désormais l’orientation. « Donner accès à un médecin, c’est important, mais donner accès au bon professionnel, au bon moment, c’est déterminant », souligne Jordan Cohen. L’intégration de l’IA en santé suit cette logique. En analysant le contexte, le motif de consultation et l’historique patient, les algorithmes sont capables d’orienter vers le professionnel le plus adapté. Cette capacité permet également d’assurer une continuité des soins, avec des relances ciblées, un suivi de l’évolution et, si nécessaire, une réactivation du patient dans son parcours. Pour atteindre ce niveau de précision, l’IA en santé s’appuie sur une diversité de données : déclaratives, issues des téléconsultations, des check-ups en pharmacie ou encore des dispositifs médicaux mesurant les constantes vitales. Toutefois, la valeur ne réside pas uniquement dans le volume, mais dans la structuration. Sans organisation, ces données restent inexploitables. C’est ici qu’intervient l’IA supervisée, qui permet de structurer l’information, qualifier les situations, faciliter l’orientation et synthétiser les données pour les professionnels de santé. Elle ne remplace pas la décision médicale, mais l’augmente avec rigueur et pertinence. « Une donnée de santé n’a de valeur que si elle devient utile au bon moment, pour la bonne décision.» Dans ce contexte, les pharmacies s’imposent comme des acteurs clés. Points de proximité, accessibles et ancrés dans le quotidien, elles deviennent, grâce à la donnée et à l’IA, de véritables hubs de santé. « L’idée n’est pas de digitaliser la pharmacie seulement pour la digitaliser : c’est de renforcer son rôle dans le parcours de santé ». Entre défis, éthique et passage à l’échelle maîtrisé Le véritable défi de l’IA en santé se joue dans l’intégration des solutions, la gestion de la donnée et surtout l’adoption par les professionnels. Car ici, plus qu’ailleurs, la confiance est un socle indispensable. Jordan Cohen le souligne : « En santé, la confiance est non négociable. La question n’est pas “qu’est-ce qu’on peut faire ?, mais qu’est-ce qu’on a le droit de faire, et comment ? » Face à ces enjeux, certains acteurs font des choix structurants. C’est le cas de Tessan, qui privilégie un hébergement des données en France, auprès d’un opérateur certifié HDS, dans le respect strict du RGPD. Et lorsqu’il s’agit de croiser IA et santé, viser un agrément en tant que Société de Téléconsultation auprès du Ministère de la Santé représente un niveau d’exigence supplémentaire. Mais au-delà des cadres techniques et réglementaires, tout repose sur une discipline d’usage. La donnée ne doit pas être exploitée simplement parce qu’elle est disponible, mais parce qu’elle apporte une réelle valeur au parcours de soin. Même logique côté IA : pas de boîte noire, pas de décision autonome, et toujours un professionnel de santé dans la boucle.Car au fond, le sujet dépasse largement l’IA. Il touche à l’organisation même du système de santé. « Aux pharmaciens : votre rôle devient central. Aux professionnels de santé : l’IA peut vous redonner du temps médical et améliorer la qualité de prise en charge. Aux pouvoirs publics : il faut soutenir les modèles qui reconnectent les parcours. » Cet article IA dans la santé : et si le vrai défi était l’organisation des soins a été publié sur LEBIGDATA.FR.

Article de Frédéric Lenfant : « De l’analyse criminelle à l’Analyse Relationnelle Visuelle »
Afin d’écrire un article pour la revue Cyber & Compliance